How to block IP ranges in Windows Firewall
If you are using Windows and have not installed a "complete" security suite for the operating system, you are likely using Windows Firewall to protect the operating system.
While there are standalone firewall applications as well, or hardware firewalls, it is likely that most users make use of the built-in firewall of the operating system.
Configuration of the firewall is not as straightforward as it can be, considering that you first need to find out how to open it, and then work your way through the menus that it makes available.
The guide that you are reading looks at one advanced configuration option: how to block IP ranges in the Windows Firewall. This is a list of IP addresses that you combine in a single expression, for instance 206.111.0.0 - 206.111.0.16 which covers all IP addresses in that range. Note: the screenshot below shows a different rule.
How to load the firewall controls
The easiest way to load the firewall controls is the following:
- Use Windows-R to bring up the run box of the operating system.
- Type WF.msc and hit the enter key.
Block IP ranges
Note: The following guide uses the built-in firewall of Windows 7. If you are using a different Windows operating system, the way may be different.
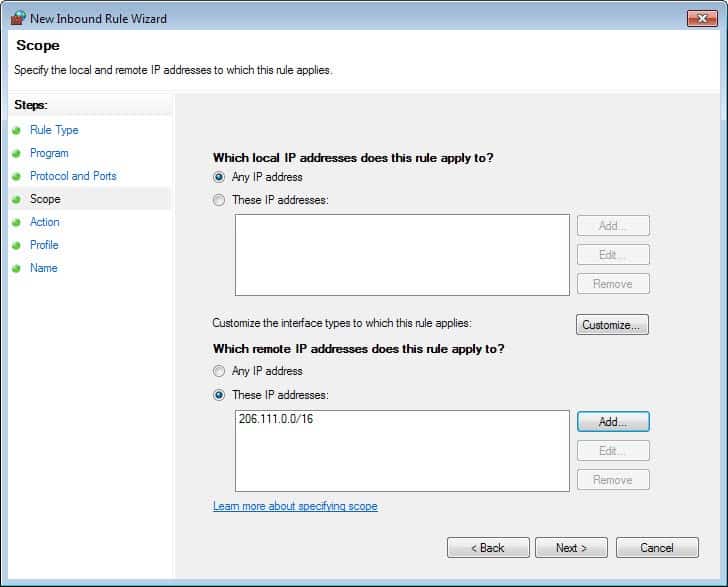
- Click on Inbound Rules on the Windows Firewall with Advanced Security window.
- Select New Rule under Inbound Rules on the right.
- Select Custom rule on the next screen and click on next.
- Leave everything as is on the screen that comes up and click next (all programs selected).
- Leave everything as is on the ports and protocols screen and click next.
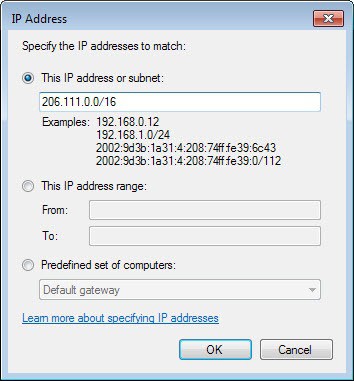
- Select "These IP addresses" under "Which remote IP addresses does this rule apply to",click add, and enter the scope in the following format: 206.111.0.0/16. This works with IPv4 and IPv6 addresses. You can alternatively use the IP address range option below instead. Note: The range 206.111.0.0/16 applies to addresses starting with the first two numbers (206.111...).
- Click ok, the IP range should now be listed under these IP addresses. Click next.
- Select block the connection on the next screen. This blocks those IP addresses so that connections cannot be established anymore.
- Leave everything as is on the next screen and click next.
- Name the new rule and add a description to it if you want.
- The new rule appears in the inbound rules list now.
Edit or Remove the rule
You can edit or remove the rule at any time. To edit it, double-click on it in the firewall controls and use the tabs to make modifications to the rule set.
To delete it, simply select it and hit the delete key on your keyboard afterwards. All you need to do then is confirm the prompt and the rule gets removed from the system again.



















You can still do it like always in windows firewall (2022). It’s not just that though. The process is not something you want to have to keep doing if you need to update the list often. There are other issues as well. But I have found that binisoft as was mentioned above at least somewhat bridges that gap.
in your exemple I will prefer 206.111.0.0 trought 206.111.255.255
but in the fire wall of windows either this system don’t work you have to use certainly
https://www.commentcamarche.net/faq/18728-configuration-du-pare-feu-avance-de-securite-de-windows-7 sorry but it’s in French let me know on my e-mail
chris.
Best regards and Many thanks for your help
On my Win10Pro, if I choose ‘custom’, I can add a scope.
This was 2014… how do we do it NOW, in 2017???? (“Scope” is no longer an option: Rule Type, Program, Action, Profile, and Name. Nowhere do I see a place that I can add an IP or a URL to block…. It seems all this POS firewall is good for NOW is to block INSTALLED PROGRAMS from running–which I can do by manually uninstalling–making this the most useless POS I have ever seen.)
Seriously?
Since when does 206.111.0.0/16 mean:
206.111.0.0 through 206.111.0.0 inclusive?
Windows Firewall is a great utility, and they have resisted the calls to include pointless outbound filtering (if something is calling out you’re already scuppered), and is really easy to use, but if you don’t get subet masks, then its not going to go well!.
I know this is an old article, but I know who you are “Alan”. You’ve been pestering the alt.comp.freeware newsgroup with your poor logic about outbound blocking for years. What part of a Trojan calling out for more malware or other such hijinks to jump onboard don’t you understand? You are acting like a fool if you honestly believe that anybody believes you and your nonsense. And now, even the company you work for, Microsoft, disagrees with you and grudgingly includes outbound blocking in their firewall.
You are right, I did not make that clear enough. Windows Firewall handles subnets correctly, my description needed more explaining.
Windows Firewall functionality is great, at least starting with Vista that included outbound filtering, but unfortunately the interface is not so great. Here’s a tip for a future review:
Windows Firewall Control – http://www.binisoft.org/wfc.php
It only uses the Windows Firewall functionality, but with a new and much better interface so you won’t have to go into the complicated “Windows Firewall with Advanced Security” interface.
It adds everything you could ever want with Windows Firewall that Microsoft didn’t build into it. For example having easy control also over all outbound connections (which is disabled by default in Windows Firewall so it allows everything!!).
How I discovered this was I wanted to enable outbound filtering but soon realized it’s almost impossible to achieve with the default interface, so I started searching info about it and found this amazing app.