Google Chrome to encrypt HTTP cookies on desktop systems: what it means
All web browsers store cookies in plain text, or in databases, that can be read with the right tools. That requires local access to the system, which means that the chance of cookie data leaking is limited.
Still, malicious software could pull the information from user PCs considering that cookie storage is usually linked to a single location on the system.
While that differs from web browser to web browser, it is not difficult to check them all and grab what you can in the process.
And if a hard drive or partition is not encrypted, it may also be possible to scan the hard drive externally to dump the information.
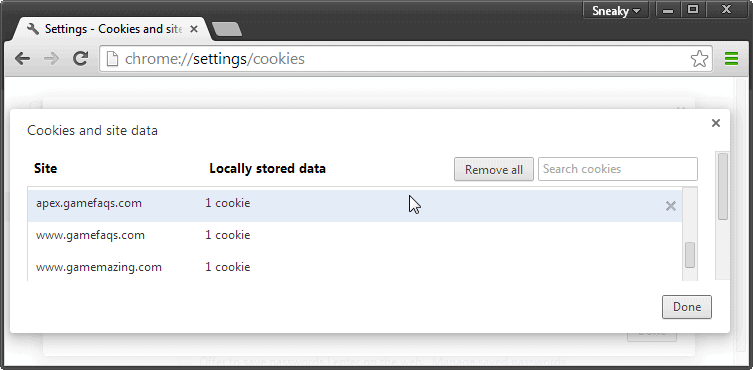
Google Chrome saves cookies to a file in the user's data folder. It is named Cookies and is a SQLite database. You can load it into any SQLeditor, for instance Firefox's SQLite Manager extension, to read all cookies that have been saved to the local system as a result of the user's Internet activities.
A recent change to Chromium has the consequence that all desktop versions of Google Chrome will encrypt stored cookies in the near future (while Chrome OS and Android use fully encrypted profiles already).
This only affects new cookies saved to the system after Chrome is updated with the new implementation. Existing cookies remain as is, while all new cookies will be encrypted by default by the browser.
According to Google, the performance drop that goes along with encrypting cookies is insignificant. On Macs, it is 1ms while Windows users may experience slow downs up to 0.7ms.
So how well is the new protection?
It needs to be noted that this won't protect cookies of a user if that user is signed in on the system. So, if you hand over your computer to another person, they may still read the cookies.
It changes things for other users with access to the operating system, and also in regards to software on external machines that scans, analyzes and transfers data from the system in question.
Say you want to analyze the computer's hard drives for forensic evidence. Depending on the level of encryption, it may be possible to dump all cookies and other sensitive information, or not.
With encrypted cookies, only the encrypted bits of data can be dumped, but not the plain text information directly.
In other words: if you are the only user of the system and use full disk encryption, then it won't add any level of protection to it.
If there are multiple users, it may protect the cookies from being snagged by other users. This too depends on the level of protection on the system.
And if you do not use encryption, it may also protect the cookies from being read by third-parties trying to transfer information from the PC to another system.
Closing Words
If you share your PC, or do not use full disk encryption, then you may benefit from this new encryption of cookies. In all other scenarios, you won't.
Advertisement

















Is there a way to disable this feature?
encryption is taking place in the browser right?If so, someone can get it before it hits the browser.
I suppose its not even in Canary yet so it will be quite a long time before it trickles down to a stable Chrome build.
The ‘playing’ marker on the tab still have yet to debut in stable Chrome.