4 Simple Password Creation rules and 6 common sense tips
Passwords are essential in the computing world: from using a password to sign in to your operating system to passwords for accounts on the Internet or accessing email.
The system is highly inconvenient from a user's point of view if basic security rules are followed, and highly insecure if made convenient, for instance by re-using the same password on all services and devices.
The following guide looks at the most important rules when it comes to the creation of passwords. If you follow all of them you make sure that your passwords are secure.
While there is still the chance that someone will be able to decrypt them or steal them, the impact that this have will be less than for the average user who may use the same password on all services.
Password Creation Rules
1. Passwords need to be strong
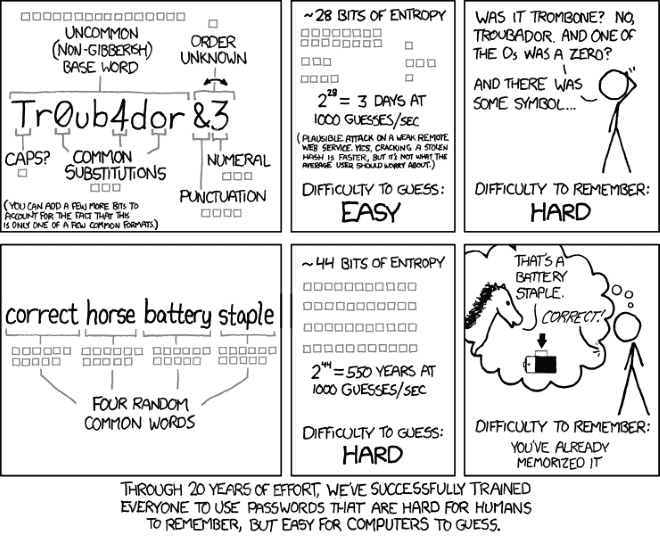
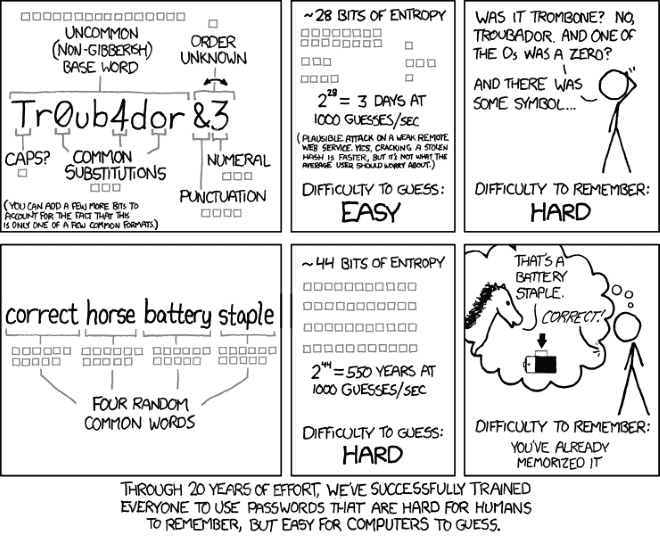
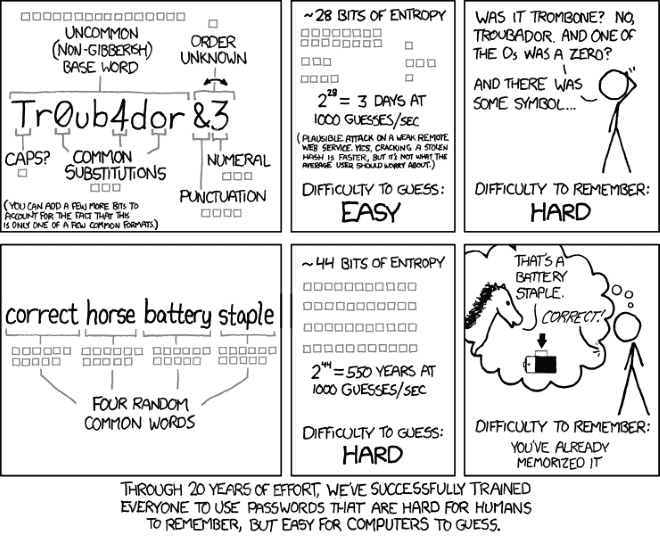
There is no definition of what strong means in regards to passwords. The general consensus is that passwords need to be of appropriate length and complexity.
I prefer to use passwords of 16, 20 or even more characters if the service allows it. Longer passwords are harder to memorize, but that is only a problem if you are not using a password manager that does that for you.
So, if you are using a password manager, you only need to remember the master password for it and nothing else. And that master password should be very secure (mine is very, very long and strong).
Strong also refers to the characters used in the password. It is best to combine
- Upper and lower case letters
- Numbers
- Special characters
to increase the strength of the password.
2. Passwords need to be unique
This is an important rule, even though it is not the most important rule. The basic idea behind making passwords unique is that if someone gets hold of one of your passwords, they can't use it for other services that you are a member of.
A single strong password that has a low probability of being stolen makes it less likely that this ever happens, even if it is the only password used by a user.
That's in theory only though, as there are means of stealing passwords without having to decrypt them first. This can be through social engineering, keyloggers, companies that store the passwords in plain-text format, or software that records network traffic.
It is also important to note that unique means also that you can't use the username or a slight derivation of it as your password.
3. Passwords can't be in the dictionary
There are two major types of attacks against an encrypted password to decrypt it. Brute-Force attacks that try every possible character combination imaginable, and dictionary-based attacks that use a dictionary file. The latter is a lot faster as it just have to go through all the words in a dictionary, and maybe in addition some combinations or additions (two dictionary words combined, or adding 1 to the end of each word).
This includes popular terms, like favorite sport teams, pet or human names, sequences on the keyboard (qwerty, asdfyxcv) or artist names, and all personal information about yourself or your family including the name of the street, your school, license plate of your car or your favorite family vacation.
4. Password Managers do all the work for you
While it may be an impossible task for most users to create and memorize strong unique passwords for every service they use, it is not really something that most users need to worry about, as password managers can do all the heavy lifting for them.
Password managers such as KeePass or LastPass help you generate and remember secure unique passwords. Even the built-in password manager of the browser can be of use. While not all come with password generation options, they do save all passwords that you create on the Internet so that you do not have to remember them all individually.
Common Sense
Along with the creation of secure passwords come guidelines that help you make sure that no one else gets hold of your passwords.
- Be cautious about public computer systems. Since you do not have full control over the system, you do not really know what is running in the background. It is best not to type your passwords on these systems at all. If you do use them, make sure you log out of all services that you have signed in during the session. I'd also recommend to clear the cache, cookies and browsing history, and to restart the computer if possible.
- Do not send your password to anyone, not your friends, family or someone claiming to be a support member of a service you use.
- If a server gets hacked, or you have the feeling that your account got compromised, change the password immediately even if it is false alarm or if there is only a slim chance that someone can actually decrypt your hopefully secure password.
- Make sure your password manager is properly protected. If you use your browser's password manager, make sure you protect it with a Master Password. If your browser (Chrome) does not have that option, do not make use of the password manager in the browser, but use another tool for it.
- Change all insecure or weak passwords if you still have any.
- Make sure the password for your email account -- the one associated with accounts you use on the Internet -- is also secure. Someone who manages to get into your email account can use the "password recovery" option of Internet services to create a new password for accounts to gain access to them.
Now Read: How secure is your password?


















Password managers are really helpful especially when it comes to generating those long and incomprehensible passwords. Anyway, they have to be so to be considered strong.
I’ve tried to brute-force my way into a password protected element using dictionaries in the past, and not once have I succeeded. Needless to say, it is a highly time consuming endeavour indeed.
Here is a very small list of some of the most frequently used passwords:-
password, 123456, 12345678, 1234, qwerty, 12345, dragon, pussy, baseball, football, letmein, monkey, 696969, abc123, mustang, michael, shadow, master, jennifer, 111111, 2000, jordan, superman, harley, 1234567, fuckme, hunter, fuckyou, trustno1, ranger, buster, thomas, tigger, robert, soccer, fuck, batman, test, pass, killer, hockey, george, charlie, andrew, michael, love, sunshine, jessica, asshole, 6969, pepper, daniel, access, 123456789, 654321, joshua, maggie,
starwars, silver, william, dallas, yankees, 123123, ashley, 666666, hello, amanda, orange…
Sometimes I use md5 or sha512 as my passwords.
It looks very secure for me.
I’d like to point to:
http://arstechnica.com/security/2012/08/passwords-under-assault/
http://arstechnica.com/security/2013/10/how-the-bible-and-youtube-are-fueling-the-next-frontier-of-password-cracking/
two articles well worth reading and few conclusions have to made
1. any password under 7 characters can be brute forced in reasonable time
2. leet-speak subsitutions are of no help.
3. stringing words together will become useless sooner rather than later, because they will fall to dictionary attacks as well
I’d say using a password manager is the only safe way to go.
Then we just have to hope for websites that support sufficiently large passwords and character sets
Great article Martin, thank you! One password manager that wasn’t listed that’s definitely worth checking out is PasswordBox. I’ve been using it on my iPhone and computer to manage my passwords and it’s free, easy to learn and logs me in to my accounts wihtout needing to type out my details. Good option for those who are looking for a better system
Being ‘somewhat’ of a romenophile, I decided to use words in Latin as my password (which by the standards of [ https://howsecureismypassword.net/ ] would take about 511 years to crack), I then capitalise all the letters in it that look like Roman numerals (8 million years), I then threw in a few numbers and symbols to separate the words and syllabi from each-other (19 billion years) and ultimately I added little ‘something, something’ which I am not going to mention here (32 sextillion years!).
e.g. – viridarium de illusio [ VIrI&Dar&IuM509de27ILLu&sIo ]
This is just one example of the multitude of password configurations that I use (I only use the aforementioned algorithm for one password), it may seem complicated to learn at first but it gets easier once muscle memory kicks in, I remember all the parameters that are use in the password because I know what they are all in reference to.
THANK YOU
If you forget your password, just hack into NSA, they have it.
They don’t need a pass to access your web accounts :)
I use similar methods to yours. Although my master passwords are a bit shorter. :)
Changing passwords occasionally is also a good idea.
That is easier to do for people who use password managers.
Keeping secured copies of passwords outside of your home in a trusted secure location (as well as all of your data) can be wise too (in case of a fire, weather events, robbery, etc).
I don’t trust cloud services to do that.
Trubador&3 is what we are stuck with because few accounts allow more than 8-10 characters.