Hushmail: why you should run the Java version
With Lavabit shut down for the time being and uncertainty whether it will get back up its feet ever again, users of the secure email service may have started to look for alternatives right away. One that is probably high up on the list is Hushmail, a long-standing email provider that is offering free and premium accounts to its users.
The free account is not really usable if you ask me, as it gets you 25 Megabyte of storage space and the requirement to log in at least once every three weeks to avoid it being shut down.
What many users do not know as well is that Hushmail is offering two different options when it comes to communication with their servers. While both use encryption to protect email from prying eyes, they differ in regards to where critical operations are executed.
If you are using the default configuration, critical passphrase and private-key operations are carried out on the Hushmail server. That's problematic as it is giving the site operators - and therefore also law enforcement and other agencies - options to decrypt user emails as they have access to the server the operations are carried out.
Wired published an article in 2007 about that and how this was exploited to collect evidence on an alleged steroid dealer.
Anyway, if you are using the non-Java way of connecting to Hushmail, you are in theory giving anyone with access to the server - Hushmail, Feds, agencies - an option to decrypt all of your messages.
The only way around this is to use the Java applet instead that Hushmail is offering. The reason for this is that the applet is run on the local computer, taking care of all the decrypting and encrypting locally, so that server operators cannot intercept the password and decrypt the emails.
A security analysis of Hushmail's regular service hints at possible attack vectors. It highlights three scenarios where your data may not be protected:
- Attacker controls the web server.
- Attacker controls the local computer.
- Attacker compromises the web server after email was accessed (memory)
The two web server vulnerabilities are not playing a role anymore if you are using the Java applet.
Enabling Java
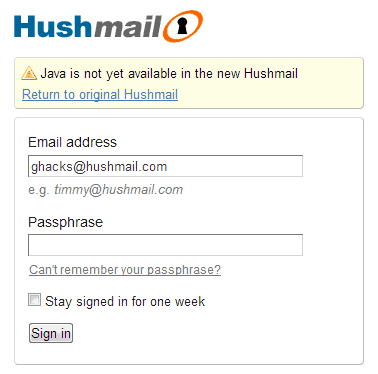
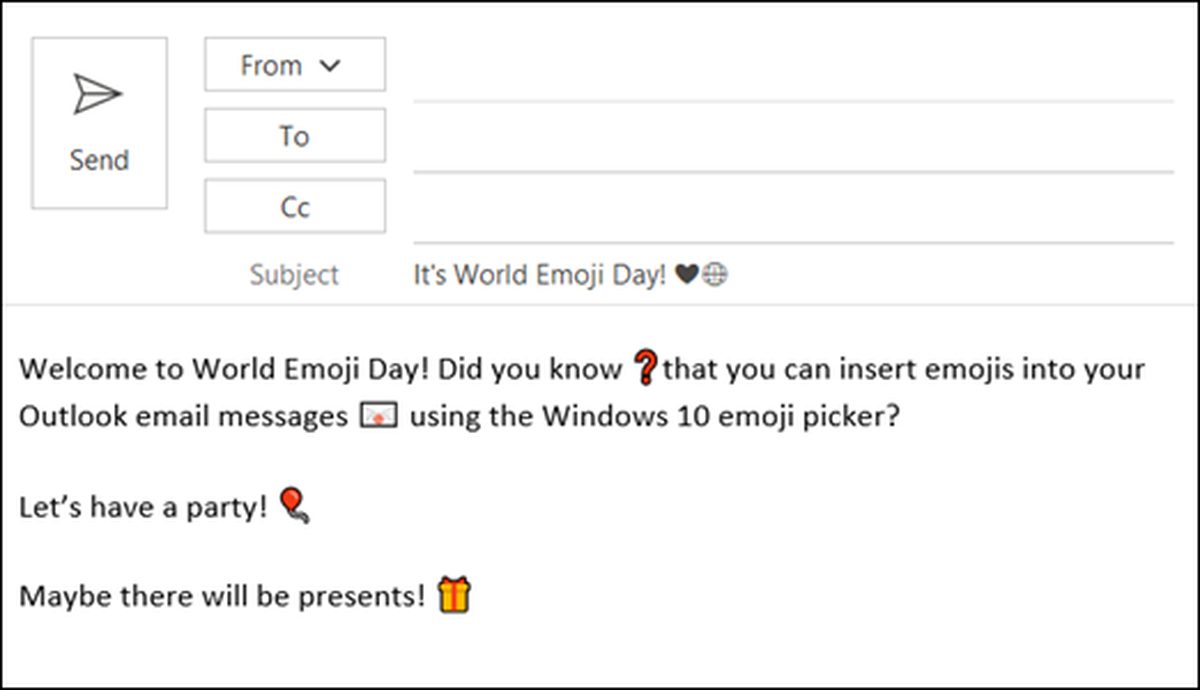
Users can enable Java when they sign in to the service. It is probably best to do this the first time you sign in to the account, but you can switch to Java - and back - anytime you want.
If you sign in on the page right away, you start to use the new Hushmail. To avoid this, click on "return to original Hushmail" which redirects you to the Java version of the email service.
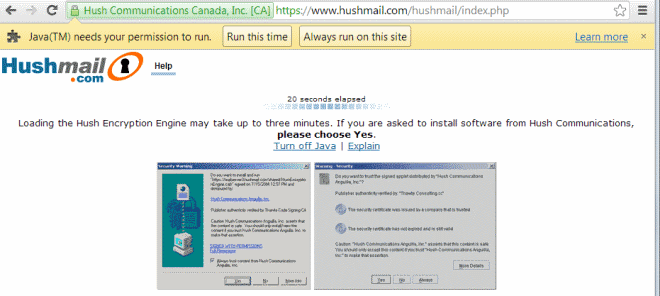
Depending on how your browser is configured, you may receive a permission request at the top of it, or a request to download and install Java if it is not installed on your system.
You may also receive a second prompt in which you are asked if you want to run the HushEncryptionEngine application which you also need to accept.
Advertisement


















I’d really like to have two step verification for EVERY time I log in; fom someone who’s had identify theft and the hacking of all of my accounts, ID prefer it.
It is said that the Java version will be no longer available after 27th April 2016. Has anyone else realised this problem?
Is hushmail still up and running? I cant access the site. IE keeps saying its not running or its gone. Someone help cuz after 3 weeks the free account expires if you dont log in every so often.
I just accessed hushmail.com without difficulty
I’m in the UK & I used Firefox.
Clear your cookies, try a different browser
I use it for a rarely used email address and never for anything sensitive.
Using the Java applet would mean enabling Java in Firefox and that isn’t going to happen.
I only have one application that requires it on my PC and would like to dump that too.
If you’re a U.S. resident, you use the Internet, or even if you don’t, the government can always access your stuff. All that it takes is a warrant. They’ll take your PC if they want.
Interesting article and comments. I planned to use Hushmail but now I don’t know more.
What I want is my IP to be hidden when I send an e-mail.
Yahoo shows it in the header…
Hushmail has previously turned over info to government. They are not to be trusted.
I suppose the below are security features :)
I can’t comment on the premium version, but the free Hushmail has no way of copying your email folders contents out of the Hushmail cloud for safe keeping. One is dependent on Hushmail reliably storing them for you. If you don’t use Hushmail for a short while [three weeks?] your account & contents are deleted & not recoverable.
If you want to email someone not on Hushmail they get a Hushmail link & have to go to Hushmail to read the message & they have no way of keeping a copy of your message on their system. [I didn’t try unchecking the “encrypted” box so maybe it’s a normal mail to the recipient if it’s not encrypted]
Also… it’s been a while but from memory I don’t think one can search the mails for keywords in the free version
why such paranoia? if you actually have any communication that you worry about being read by “Hushmail, Feds, agencies” then you should be encrypting it before it leaves your computer anyway.
for the average user, hushmail with or without java is great— also the Hush Secure web forms are helpful when you need to pass sensitive info like c.c. numbers, etc. to someone that does not use OpenPGP.
Uh, Hushmail is not a secure email service.
People used Lavabit because of its ideals and frankly because it was a good-quality email service. Hushmail has openly admitted it gives up all data to the Government, even without a warrant. It also holds the encryption keys so it is in no way any safer than say Hotmail or Gmail. Just cause something has encryption, doesn’t make it secure.
I am switching to yandex, any comments on yandex regarding privacy
Silent Circle closed Silent Mail.
http://silentcircle.wordpress.com/2013/08/09/to-our-customers/
… Today, another secure email provider, Lavabit, shut down their system lest they “be complicit in crimes against the American people.†We see the writing the wall, and we have decided that it is best for us to shut down Silent Mail now. We have not received subpoenas, warrants, security letters, or anything else by any government, and this is why we are acting now…
Nice review, Martin and although using the Java version may seem more secure, I uninstalled Java a long time ago and refuse to re install it!
Mozilla will only disable it in Firefox, anyways!
As you stated, the Free account is not really useable, so why bother?
MEGA will be releasing their Free encrypted e-mail in early 2014, according to Kim Dotcom, which seems like a better alternative!
Damn Government keeps sticking it’s nose where it don’t belong, invading our privacy, which is criminal on their part!
When is all this nonsense going to stop?
As I’ve read, law enforcement could ask Hushmail to inject a ‘back-door’ of some sort in the applet to be able to decrypt the communication, and I understand Hushmail has made it clear that it would have to comply if asked.
They all have to abide by the law. If you’re suspected of dealing drugs and an agency can show probable cause then expect to get pwned. Read their policy, it states clearly what is required in order to divulge your info.
The difference is that HushMail and others like it require more than a rubber stamped warrant from a secret court or a “friendly request” from the feds.
Here’s a few alternatives that someone posted on Reddit. I’m not familiar with any of them but they might be worth checking out:
NeoMailbox (Switzerland) or Countermail (Sweden) or The SilentCircle mail app (Servers in Canada I believe)