Evernote hacked: resets all passwords
The note-taking service Evernote has posted a security advisory on its website informing the public that the company's Operations & Security team has discovered - and blocked - suspicious activity on the Evernote network.
An investigation of the matter revealed that the attackers managed to download user information, usernames, email addresses and encrypted passwords but did not access data stored by users on Evernote's servers.
The company made the decision to reset all user account passwords as a precaution. The past has shown that brute force attacks on dumped password databases will return a large number of valid passwords in short time. By resetting all passwords, Evernote blocks the attacker from accessing the accounts using those decrypted information.
With the passwords being unusable to gain account access, hackers are left with a database full of usernames and email addresses. It is certainly possible that the information could be abused by sending out emails to customers claiming it is coming from Evernote to trick them into visiting a malicious website.
Evernote has sent out emails to all of its users informing them about the security breach. While that is reasonable, considering that the majority of users are probably not reading security advisories that the company posts, the team that created the email made a major mistake according to the Naked Security blog.
Both the security notice on the Evernote website and the email give the following sound advice:
Never click on 'reset password' requests in emails — instead go directly to the service
The email that Evernote sent out contains a password reset link that the company added to it. To make matters worse, it does not link directly to an Evernote server, but uses an email marketing domain as a redirect which makes it look like a phishing link.
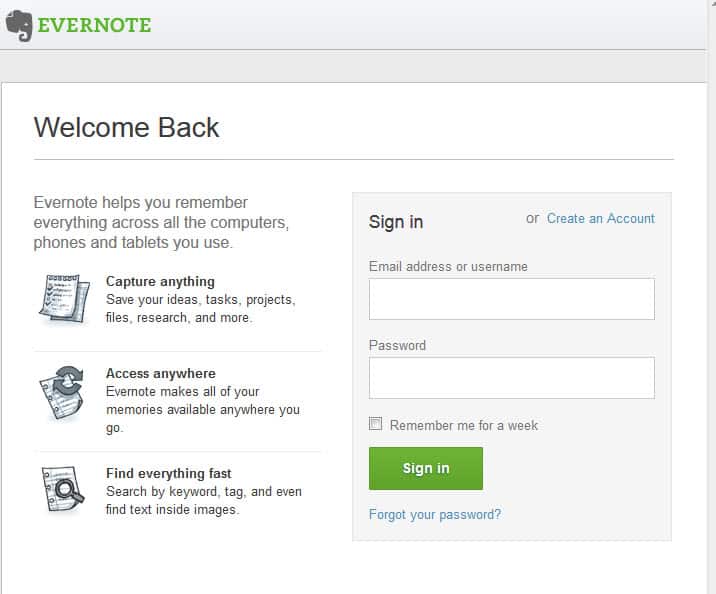
I'd recommend to visit the Evernote website directly using your web browser of choice to select a new account password for the account.
It is recommended to change the account password on other websites as well if you have been using the very same password for your accounts on these sites.
Advertisement
















Does anyone really even use evernote, NEVERNOTE sounds like a better name.
Forgot to add, with your own keys, not those of the service.
At the very least anything stored on the cloud should be securely encrypted.
Resetting the password isn’t enough. Users must change their user-name and their email address, used everywhere, as those have been already sold to spammers.
Lorenzo, this is why one must never upload private data on network.
Cloud computing.
—–
Both the security notice on the Evernote website and the email give the following sound advice:
“Never click on ‘reset password’ requests in emails — instead go directly to the service”
The email that Evernote sent out contains a password reset link that the company added to it. To make matters worse, it does not link directly to an Evernote server, but uses an email marketing domain as a redirect which makes it look like a phishing link.
——
>> insert Picard, Riker Double Facepalm here <<
Kind of like the business (true story) who would send out forms to people and in bold letters that the beginning of the form asked them to fill out the form with a BLACK pen. And they were kind enough to sent out a free pen with every form. Only problem was that it was a BLUE pen. And they did that for almost five years (because they wanted to give away all the pens)
This is why we have not upload private data on network :/
This type of attacks and viruses are becoming so much common. Every now and then there is an email saying ‘PayPal need more info’ etc. But we see so much less efforts to tackle these situations.
All 50 million users data has been downloaded.