Microsoft Security Bulletins For July 2012 Released
Yes, it is that day of the month again: Microsoft Patch Tuesday is here and it delivers nine security bulletin covering 16 vulnerabilities this time that fix issues in the Windows operating system and other Microsoft products such as Microsoft Office, Internet Explorer, Microsoft Sever Software, and Microsoft Developer Tools.
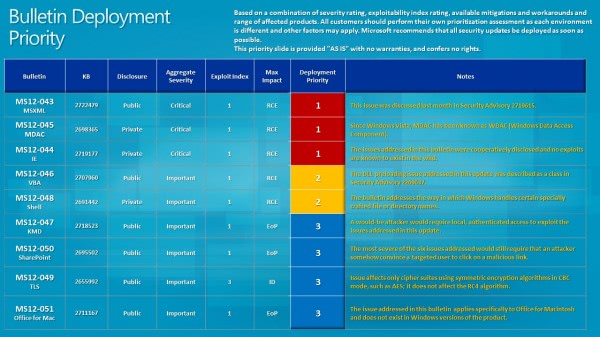
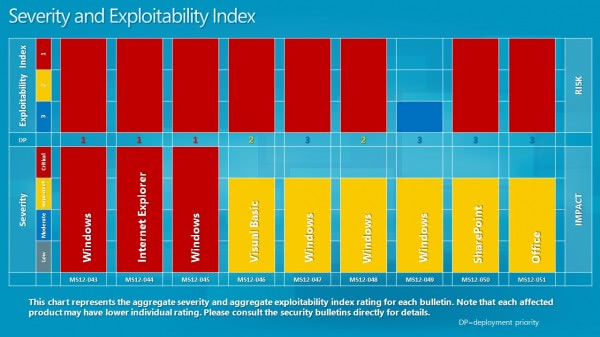
Three of the bulletins have received a maximum severity rating of critical, the highest possible rating, while the remaining six a rating of important. Maximum severity rating means that at least one product or product version is affected in that severity.
As far as the deployment priority goes, Microsoft recommends to deploy fixes for MS12-43, 45 and 44 first, before deploying MS12-046 and 48, and then the remaining 47, 49, 50 and 51 bulletins.
Bulletin Overview
- MS12-043 Vulnerability in Microsoft XML Core Services Could Allow Remote Code Execution (2722479) This security update resolves a publicly disclosed vulnerability in Microsoft XML Core Services. The vulnerability could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker would have no way to force users to visit such a website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes the user to the attacker's website.
- MS12-044 Cumulative Security Update for Internet Explorer (2719177) This security update resolves two privately reported vulnerabilities in Internet Explorer. The vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS12-045 Vulnerability in Microsoft Data Access Components Could Allow Remote Code Execution (2698365) This security update resolves a privately reported vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if a user views a specially crafted webpage. An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS12-046 Vulnerability in Visual Basic for Applications Could Allow Remote Code Execution (2707960) This security update resolves one publicly disclosed vulnerability in Microsoft Visual Basic for Applications. The vulnerability could allow remote code execution if a user opens a legitimate Microsoft Office file (such as a .docx file) that is located in the same directory as a specially crafted dynamic link library (DLL) file. An attacker could then install programs; view, change, or delete data; or create new accounts that have full user rights. If a user is logged on with administrative user rights, an attacker could take complete control of the affected system. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS12-047 Vulnerabilities in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege (2718523) This security update resolves one publicly disclosed and one privately reported vulnerability in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker logs on to the system and runs a specially crafted application. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability.
- MS12-048 Vulnerability in Windows Shell Could Allow Remote Code Execution (2691442) This security update resolves one privately reported vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if a user opens a file or directory with a specially crafted name. An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
- MS12-049 Vulnerability in TLS Could Allow Information Disclosure (2655992) This security update resolves a publicly disclosed vulnerability in TLS. The vulnerability could allow information disclosure if an attacker intercepts encrypted web traffic served from an affected system. All cipher suites that do not use CBC mode are not affected.
- MS12-050 Vulnerabilities in SharePoint Could Allow Elevation of Privilege (2695502) This security update resolves one publicly disclosed and five privately reported vulnerabilities in Microsoft SharePoint and Windows SharePoint Services. The most severe vulnerabilities could allow elevation of privilege if a user clicks a specially crafted URL that takes the user to a targeted SharePoint site.
- MS12-051 Vulnerability in Microsoft Office for Mac Could Allow Elevation of Privilege (2721015) This security update resolves one publicly disclosed vulnerability in Microsoft Office for Mac. The vulnerability could allow elevation of privilege if a malicious executable is placed on an affected system by an attacker, and then another user logs on later and runs the malicious executable. An attacker must have valid logon credentials and be able to log on locally to exploit this vulnerability.
Updating
As usual, it is recommended to update as soon as possible. Windows Update is already listing the updates, and users who have not configured their operating system to update automatically, or have started their PC earlier today, can check for updates manually there to find and install them on the PC.
Users who prefer to manually update find the bulletin downloads over at Microsoft's Download Center where they can be downloaded and deployed to (multiple) systems. The July Security ISO will be available on the site shortly as well.
Advertisement

















I also had problems with windows upgrade today, had to reboot the computer 3 times before it behaved normally. I have Windows 7 x64 Home Premium. Have never had any problem before this update today 2012-07-11.
In 2 month we will see the added Windows 8 , Windows RT in the list of security patches. We will be to judge how much of a copy & paste from Win 3.1, 95, NT, 2000, XP… have been ported to Window 8/RT .
Look at the XML patch MS12-43 where the code has been copied without any QA for years and effects :
XP, Vista, W7, 2003, 2008, 2008 R2, Office
2003, Office 2007, Office Word Viewer, Office Compatibility Pack,
Expression Web 1, Expression Web 2, Office SharePoint Server 2007, Office
Groove Server 2007
MS12-046 fixes a security hole that has been patched in the past tens of times…..
Thanks for your effort this mouth again. Every mouth it makes so much easier to understand what is happening with main updates that month.
This month again 13 updates.
link for Microsoft’s Download Center is wrong
http://www.microsoft.com/it-it/download/details.aspx?id=30313
Hi,
Had a BSOD as well!!! HP Elitebook running Windows 7 x64. Never had any problem with this computer before. I’m the IT manager of the company, so I take good care of my tools…
Hope it won’t happen to all of my users or it means serious trouble.
WTF!?!?!
Update notification on both 7 Pro 64 computers here listed 8 important, no critical or optional and some were different from those listed above.
Installed all 8 first on the HP HDX X18T-1100 CTO Premium with no issues. But it has an OEM 7 Pro clean install that wiped all HP stuff followed by carefully selected driver d/ls from the HP site. Could that explain the difference in our update results?
Did event viewer give any clues? Or NirSoft BlueScreenView?
Anyone else got a BSOD on reboot after applying these updates? I had to restore my system
No problems. Win 7 64 bit.
I did not, Windows 7 64-bit.
Same here. Updates went as planned and all is well! :)
Just got 12 updates, mostly security patches and fixes.
The two optional updates, not installed, are Silverlight, which is useless as well as Bing Desktop!
All is well!