Bitlocker, a Guide for the Uninitiated
BitLocker, first introduced with Windows Vista, is a full drive encryption technology that works with hardware in compatible computers known as a Trusted Platform Module (TPM chip). It offers enterprise-level data encryption and caused some controversy when it first appeared with some governmental agencies calling on Microsoft to leave them a back door in, something Microsoft flatly refused to do.
If you have a laptop computer with a TPM chip then using BitLocker to encrypt the content of your hard disk is a very worthwhile activity, especially for work computers where you may be carrying sensitive personal data on staff or customers, or where any data you are carrying will be subject to local data protection regulations anyway.
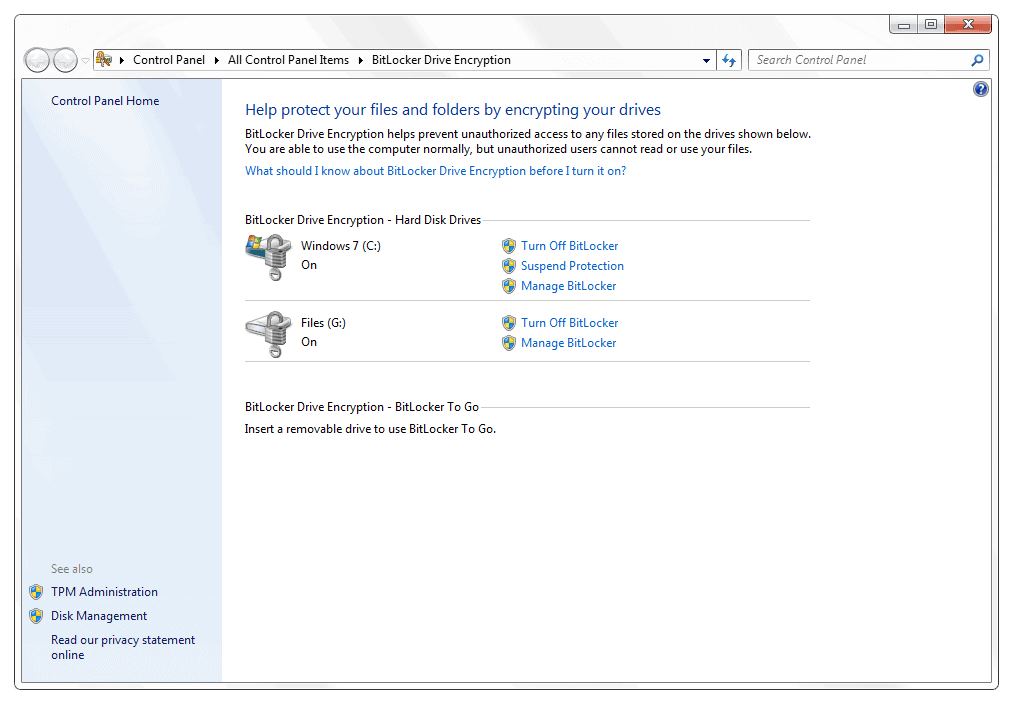
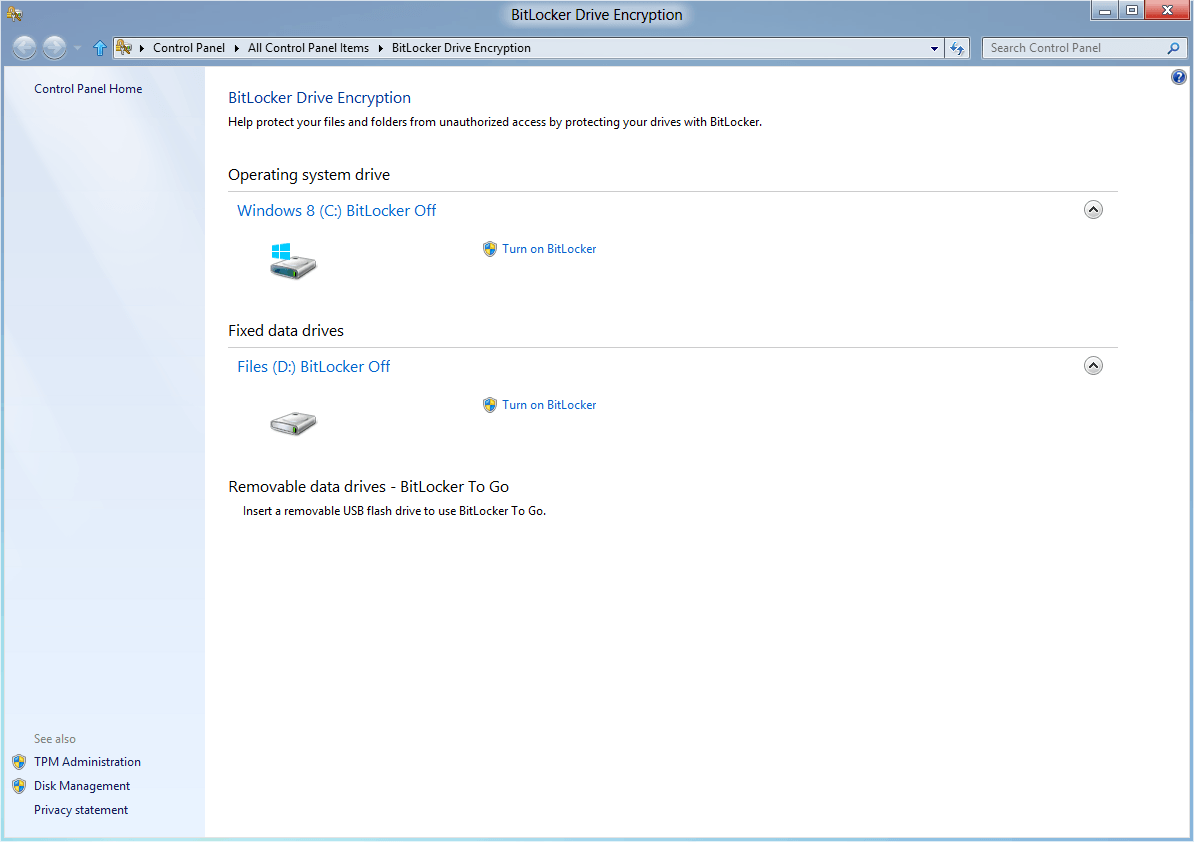
Bitlocker is easy to use too, you just go into the BitLocker option in the Windows Control Panel, select your hard disk(s) you want to encrypt and, if your computer has TPM chip, turn it on. But what atre the problems and pitfalls of using BitLocker?
Bitlocker will work very effectively and silently in the background and you won't even realise it's there. This can cause problems should something go wrong with Windows and you need to either restore it from a backup, or reinstall it completely.
When you encrypt your disk with BitLocker, Windows will prompt you to store a copy of your encryption key on a USB pen Drive. There are good reasons for this and it's wise to keep a copy of the encryption key on that Pen Drive and keep the drive itself somewhere safe but handy. Obviously if you're taking a laptop out and about you shouldn't keep the Pen Drive with you at all times where it could be stolen with the laptop, this is almost as bad as having no encryption at all.
If you need to restore Windows from a backup image however Complete System Restore in Windows will ask you for a copy of the encryption key before it can work with your hard disk(s). It will happily look on Pen Drives and find the appropriate keys. Without these keys the restore process simply won't work at all, neither will any the startup repair options in Windows 7.
When you come to reinstall Windows the problems will be worse. Before you can do this it is extremely wise to completely decrypt your BitLocker-protected drives; a process that's probably best left running over-night. You can create yourself all types of security problems if you try to reinstall Windows 7 over a partition that's already encrypted, or if you wipe the original partition and recreate it and have a second partition or disk for files.
A BitLocker encrypted disk is tied to the boot loader of a Windows installation, and it is this that it looks for to check it's not been modified before the TPM chip releases the decryption key. It would be too easy to reinstall Windows and then find you no longer have any access to your files and data because they're encryped and not backed up in an unencrypted form somewhere safe.
Backups are essential when you are dealing with any form of file or disk encryption, even Windows EFS (Encrypted File System) which I personally hate as it strips useful metadata out of files when it compresses them for reasons that make no sense. You should always make sure there is at least one fully unencrypted backup copy of your files stored in a secure location.
I would also recommended keeping a copy of your encryption key in a safe location, perhaps Microsoft's SkyDrive service. It wouldn't even matter here if hackers gained access to your account and downloaded the keys, as without physical access to the computer they relate to, the keys are completely useless to them.
So while BitLocker is a fantastic idea and one that I use on my own laptop paired with a fingerprint scanner, you need to be very careful when putting it into implementation.
Advertisement



















A backup from windows will backup the data unencrypted (such as running an Acronis backup from windows). That’s fine. Doing a bare-metal restore from that backup concerns me, however: what happens with the boot sector in that case? If you do a bare-metal restore, will the backup software re-write the boot sectors?
My old pc doesnt have tpm, but you can enable Bitlocker so it uses a flash drive instead, a little like an ignition key for a car.
I have a Lacie flash drive that actually looks like a key on my keyring and use this to start my desktop pc (and laptop). Obviously if im going out, i’ll take my keys so even if someone were to break in and steal my desktop, it’s of no use to them.
As you said though, the encrypting and decrypting aspect is a pain, as it’s VERY slow, especially with the size of drives increasing these days. I hope they find a way to speed it up in Windows 8.