Zero-Day Attack Protection Using Threatfire
The most important aspect of a good antivirus program that is essential for proper PC security is that it is consistently updated to recognize new threats. Malware changes constantly and so does the security to protect against it. Threatfire is an excellent free utility that detects potential malware threats running in the background. It does not cause conflicts with existing malware protection software and is not a replacement. It does offer the advantage or recognizing zero-day attacks.
Malicious code will exploit security holes in operating systems, programs and applications. These are security exploits which are unknown to the vendor of your existing anti-malware software. Certainly, these security exploits will be soon recognized and antivirus security software will be updated, but what do you have to defend against freshly-born threats meanwhile? By employing ActiveDefense technology using behavior analysis, Threatfire will catch potential threats before your anti-malware software has updated the signature database.
Threatfire is a simple installation and is offered free to home users. Again, there is no conflict with existing antivirus software, so you won’t need to bother with disabling applications or creating exceptions in most cases. The installation link is: http://www.threatfire.com/
Always create a restore point prior to the installation of any new software. Set the restore point before downloading Threatfire.
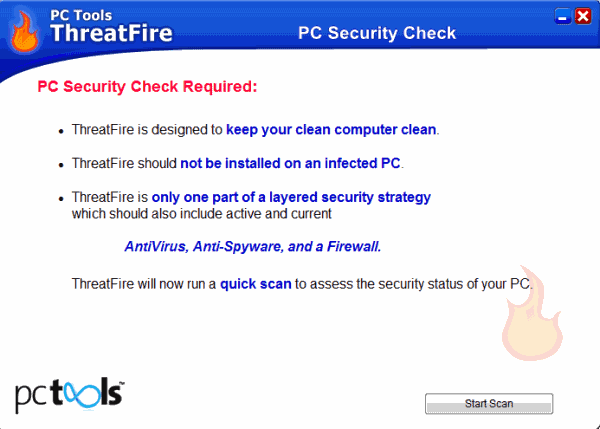
Click Next to proceed. Accept the License Agreement, choose destination folder for the installation. You can go with the default folder to keep things simple. Besides, you set your restore point, right? The program opens automatically, presenting the following screen:

Click Start Scan and ThreatFire will run a quick scan. The program detected that the Windows Firewall has not been active on the system. In addition, twelve minor threats (tracking cookies) were detected on the system.
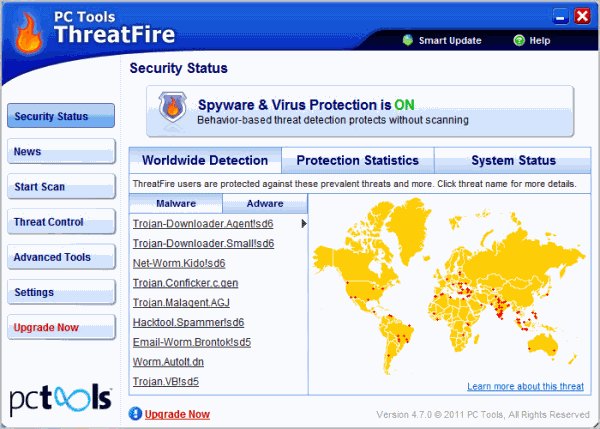
After installation, Threatfire will be running in the background to detect potential threats. As this is the free version, it will often prompt you to buy other third party software. This can be annoying, but should you decide to purchase them, you may do so and upgrade to the full version. As long as you have good anti-malware software installed on your computer, there is no need to move to the full version.
An interesting feature with Threatfire is that it will display the World Wide Detection Map, indicating the most recently identified threats detected in the community. You get an alert screen when a threat is found.
Run a full Scan
From here, run a full scan by clicking Start Scan. The scan will, of course, take some time.
The color-coded alerts indicated various degrees of threats. A yellow alert is used for potentially malicious software threats, while a red alert indicates that a malware application has been disabled and quarantined.
Threatfire opens your default web browser and opens the ThreatExpert page which details the information about the threat that was disabled. This is an interesting feature. It is always good to be educated about malware threats.
This is like a first-alert system. It is easy to operate, though some using x64 systems have had problems with it. The problems have not been major, just that the program has not worked well for everyone. For many other users, this has come in handy. The user demonstrating this article has certainly found it to be a handy addition to a PC security line-up.
Verdict:
Threatfire is a free program. The developers are not shy to advertise upgrades in various locations. New users should take note that the installation tries to install the Google Toolbar on the system. The toolbar needs to be unselected during installation to avoid this from happening.
Advertisement




















sorry for this second comment
Proactive defense against both known and unknown threats by trojans as well as viruses, worms, spyware, rootkits and other malware.
Version 4.7.0.53 is now available here:
http://www.pctools.com/forum/showthread.php
Make sure you scroll down to post #2 and click on the link.
source gizmo
thanks
nice tool , have been using with MSE and it is good
A final note: EP_X0FF of KernelMode.info is one of the foremost experts on antimalware products. Here at the link is his review of Threatfire(Threattrash) from January of this year – http://www.kernelmode.info/forum/viewtopic.php?f=11&t=586
Symantec’s take over of PC Tools made for ThreatFire/Cyberhawk’s second time at being taken over by a larger company. Off the top of my head I cannot recall a single antimalware product which has been improved upon after being taken over by a larger company even once, much less twice.
I really have a hard time recommending Threatfire. The program has been sporadically upgraded ever since Symantec took over PC Tools. Let’s not forget that Threatfire is on its third iteration as it was originally CyberHawk, then Threatfire under PC Tools and now under Symantec. It’s a program originally meant for XP users and Vista ended Cyberhawk’s run. But once taken over by PC Tools there were immediate problems, such as users being locked out of their keyboards on Vista. I’m not sure if that problem ever was fixed or just ignored until Windows 7 came along.
Problems can arise when conflicts are not addressed with bug fix releases and that problem is compounded when Windows operating systems are updated, which can create more conflicts, especially with anti-malware apps that hook deep into the system as Threatfire does. That’s not even addressing the issue of ever evolving zero-day malware threats that continuously try to find a way to circumvent programs like HIPS and behavior monitors/ soft HIPS such as Threatfire.
My advice would be to forget about Threatfire for now. If a person wants to use a third party app in their layered defense strategy then it’s better to try a free program like SpyShelter or a paid program such as Mamutu from Emsisoft or Prevx 3, although Prevx has been taken over by Webroot the program is still developed and is to be incorporated into Webroot products. If none of those programs suffice then try a firewall with a built in HIPS component such as Online Armore (free or paid), Comodo (free) or Private Firewall (free) from Privacyware.com. At least those programs are consistently updated and upgraded to fight zero day malware and whatever conflicts which may arise on computer systems.
BTW- two issues of note: 1. the latest version of Threatfire is not on threatfire.com’s download page but in the user forum as there is a direct link there (released nearly six months ago). 2. If a person has issues with the resource usage of Threatfire, an oddity of the program is that the higher the “sensitivity” level the less resources the program uses.
The core engine is not changed as frequently
as some other security products and because
of how it works it does not need to be changed,
Database updates within the program are daily.
Threatfire doesn’t appear to have been updated for over a year. I understand it functions differently, but has development stopped?
ThreatFire has come through for me
when other security tools failed.
It is an absolute must-have.
Your excellent article on this
superb tool will help spread the word,
ThreatFire should have higher awareness.