CloseTheDoor, Identify Local TCP, UDP Listening Ports
One of the things that I to regularly on all of my computer systems is to check each system's open TCP and UDP ports. It is a security precaution to make sure that only needed ports are listening, and that all other ports are closed to reduce the chance of a successful attack. I have been using various programs for that task, the previously reviewed CurrPorts by Nirsoft for instance. Today I'm going to review CloseTheDoor, another program that Windows users can use to identify local TCP and UDP listening ports.
The program is offered as a portable version and installer by its developers. Both versions offer the same functionality in all other aspects.
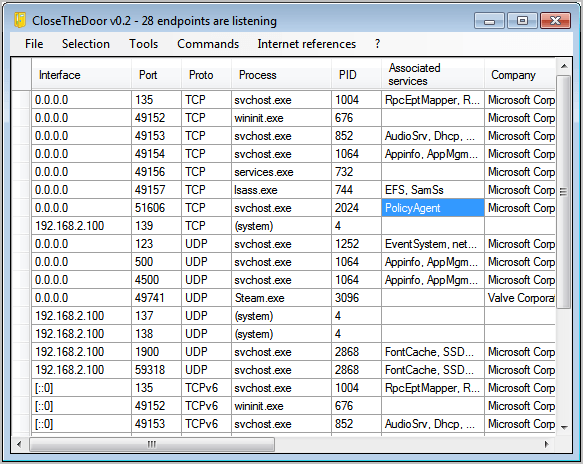
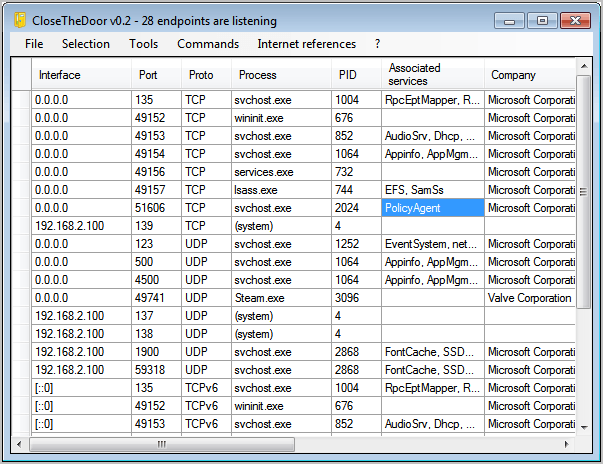
The software displays all listening ports, their protocol, process, process ID, associated services and company in the interface. This makes it relatively easy to identify specific ports directly in the program interface. Especially the associated services column can be helpful in identifying the responsible Windows services.
A right-click on a row opens a context menu with additional research options.
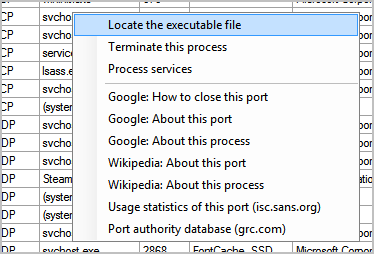
- Locate the executable file - Opens the folder that contains the process executable.
- Terminate this process - Terminates the process directly. May only be temporary if the process restarts automatically.
- Process services - Displays all services that are linked to the process.
- Google... - Research the port, process on Google.
- Wikipedia... - Research the port, process on Wikipedia.
- Usage statistics of this port - Look up statistics
- Port authority database - Provides information about most ports.
The menubar on top links to additional tools, commands and references. The tools menu links to Windows apps like the Services managements interface, the Task Manager, Registry Editor or Local Security Settings. Commands can run the netstat command to display all open connections, the task list and the system's environment variables.
Internet references finally links to essays and white papers about ports and online security. Linked there are for instance BlackViper's excellent website that is offering services configuration suggestions, lists of common port numbers or a Microsoft guide on how to configure a firewall for domains and trusts.
It is furthermore possible to display a short summary, and to export the current port list in detail. CloseTheDoor offers everything that one could hope for when analyzing open ports on a Windows machine. It is a solid alternative to CurrPorts. The software is compatible with all recent versions of the Microsoft Windows operating system. It tested fine on a 64-bit Windows 7 test system. Downloads of the portable version, installer and source code are available at the project website over at Sourceforge.
Advertisement




















I highly recommend and use portable Process Hacker and System Explorer.
Yep, you did. : )
https://www.ghacks.net/2011/01/22/tcpeye-network-monitorin-software-with-virustotal-integration/
George – You can find the portable version here – http://sourceforge.net/projects/closethedoor/files/v0.2/
@Martin – Another similar app which I use is TCPEye
TCP Eye is a great app as well, think I have reviewed it before here on Ghacks.
Don’t see any mention of a portable version. What am I missing?
Good stuff. Its always a good idea to know who is “listening in”
Good post, Martin.
I particularly applaud the listening ports security precautions that you take to reduce the possibilities of attacks.
As users, we are not entirely unable to monitor our vulnerabilities, much as we are free to explore and tap the countless online opportunities — in the form of applications, program and software — to empower our business.