What To Do When Your Email Account is Compromised
I see more and more spam coming from the email accounts of contacts and friends when I open my e-mail program. In addition to this, people are telling me that they think their e-mail accounts have been hacked.
Signs can be friends receiving messages you did not send, mail is "marked read" that they never saw, settings are changed, or anything else out of the ordinary. In any case, the question is the same: "What do I do?"
While many Ghacks readers may know to follow these steps, having a guide handy for others is a useful thing. I can imagine many readers are resources for friends, family, and coworkers. These steps can serve as a checklist to ensure thoroughness.
This is a guide on how to reasonably secure your e-mail account. What to do if you lose access to your account is a different problem for another article. This article assumes you still have access, but strange things (as mentioned) are going on. It will cover the three most commonly used e-mail account types: Gmail, Hotmail, and Yahoo Mail. While changing the settings is pretty easy, finding them can be less than obvious. Here are some screenshots to help you find the general settings page for your account.
Step 1 : Change Your Password
You need to do this immediately. This is akin to changing the locks on your doors. When you do not know exactly who has a key to your home, the locks are a liability. Count yourself lucky that you can get into your account. To change your password, log-in and go to Settings. Then follow the steps appropriate to your account.
- In Gmail: Mail Settings > Accounts and Imports > Change Password
- In Hotmail: More Options > Account Details (look for "Change" next to password)
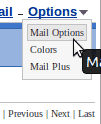
- In Yahoo Mail: Mail Options > Account Information > Change your password
The password needs to be super-secure, and I suggest you use a password manager such as KeePass to generate and store it.
If you cannot get into the account anymore, e.g. because the hacker changed the email password or because it was locked by the email company, contact the company directly to get it reinstated.
Step 2 : Check Your Recovery E-mail Address
Your recovery e-mail address is the one that you use to reset/regain your password. However, if it was changed, it can be used to get the password to your account. Take a look to see if it is set to another account you own. If not, change it immediately. You also may want to follow these steps on that account.
- In Gmail: Mail Settings > Accounts and Imports > Change Password Recovery Options
- In Hotmail: More Options > Account Details (look for "Remove" next to an odd e-mail)
- In Yahoo Mail: Mail Options > Account Information > Update password-reset info
Step 3 : Change Your Hints
Most people forget about this, but it is a good idea to change your hints. If the hacker knows the answer, they may be able to regain access. This usually requires the recovery e-mail address to be altered, but it is still better to change your hints. Since hints are usually used to reset passwords, they can be used to change your password.
- In Gmail: Mail Settings > Accounts and Imports > Change Password Recovery Options
- In Hotmail: More Options > Account Details (look for remove next to a question)
- In Yahoo Mail: Mail Options > Account Information > Update password-reset info
Step 4 : Check Your Forwards
Checking your forwards is going to be a tedious process, but it is important. If you only have time to skim them over, then do so but make a thorough look your next priority. Your bank account may depend on it. Your e-mail account can be set up to send letters to other e-mail accounts. Most websites are set up to send new passwords to your e-mail address. That means that an unscrupulous person could ask the site for your password, set up your account to forward it to an account they have access to, and the get into the site. That could be a bank site, a blog, FaceBook, or anything else.
- In Gmail: Mail Settings > Forwarding and POP/IMAP
- In Hotmail: More Options > Email forwarding
- In Yahoo Mail: Mail Options > POP & Forwarding (note: a premium service)
While you are at it, also check filters if the service supports that. On Gmail, you'd go to Settings > Filters and Blocked Addresses to get a list of all filters. Filters may also be used to process emails automatically, e.g. to forward them to another account automatically and skip the inbox.
Step 5 : Change All Your Passwords on Connected Accounts
Sadly, you have to assume that your forwards are compromised. You are going to have to go through each site you used your e-mail account to sign up with and change the password and hint provided that you used the same password.
You might even want to associate them with a separate account to isolate critical e-mails. Alternatively, you could just change your password and hint on sensitive sites. Your bank and any financial websites should be first. Social networking site like FaceBook and Twitter should be next.
Keep in Mind
You should always use a strong password for your accounts: one with uppercase, lowercase, numeric, and symbol characters. Ideally, you should have a different one for each account. At the very least your e-mail, financial, and social networking sites should have separate passwords. Security is not about absolutes, but about making it difficult for others to gain access to you account.
It is worth noting that each of these services has an extra security feature. You can actually set up your account to use your phone for e-mail recovery. As I have not used it, it is beyond the scope of this article, but is worth considering.
Additional resources
- Find out if your email address has been sold
- How to change your primary Microsoft Account email
- How Web Accounts Get Hacked




















It’s very sad how people can be so cruel heartless after you have open the doors from your home and heart!! My e mails were compromise by some one the I wouldn’t never thought he would hurt me! My ex boyfriend! I help this guy in many ways and loved him and he end up doing this and using me and many ways!!;'( I just wonder if people are not afraid of GOD and Karma!! They go from place to place using people in there convince with no kind of regret and morals!!! GOD BLESS HIM!!! N hope he appreciates good people in the future the might wanna help him!!
My account has been compromised and Yahoo has been non-responsive. I am randomly logged out while attempting to send an email, or change to another folder. Work is lost and I receive email allegedly sent by folks in my contact list which they have never sent. I have reset my password several times… Worse I have created a SEAL which is of no effect whatsoever. The idea of the seal is that a user should be presented with that seal as a verification that they are on a legitimate Yahoo site, but I can’t get that. It’s time to move to another carrier.
My email password has been changed without my permission. ex-friend change it . I can’t remember my security answer and now I can’t get my e-mail from my teacher at school. all my class work is on e-mail please help get this corrected so i can change my password or change my e-mail address. Thank you, April
Sorry i make myself very clear. I have not submitted any info to these people but i have replyed to tell them to ****off. I do feel like i have been attacked
I’m so confused, i have been getting a ridiculous amount of spam +blag email in my yahoo account. Then i get a finally warning from yahoo (no 1st or 2nd warning) informing me in with the most awfull grammer that my account will be terminated if i do not provide them with my; email address, password, country, +date of my last log in. I emailed yahoo via that address +i posted several comments on the yahoo feedback page. Now i cannot send or recieve emails from my yahoo account. Do u have any idea what is going on.
This looks like as if you have been attacked. If you have submitted your name and password to a third party, they have probably taken over the account. You need to contact Yahoo directly to resolve the situation.
If you do not have access to your account or the backup account (and you never set up the text message confirmation), then you are almost out of luck. All you can do is contact their tech support and be prepared for a lot of questions and a long wait until you get your account back.
What if I no longer have access to my Yahoo! e-mail account, yet the account somehow seems active and more importantly, I want to regain access to the account. By the way, according to Yahoo! the e-mail account in question was likely compromised. Am I to assume that Yahoo! is fixing the security problem and that the account will be accessible again?
You missed one:
– If you are using a disposable email address (like those from Spamex.com), just delete the email address. If it is tied to a forum or something that you regularly participate in, reallocate a new address and replace the old email addr with the new one.
I only give my real email addr to a very limited number of people. I do not get any spam on that addr.
Everyone else gets either a disposable email addr or one of my gmail addr.
A good point, but most of the people who I encounter with these problems don’t have such accounts. It is an idea worth introducing to them, but I know several people that it would confuse. That said, it’s a perfect thing to point out in a comment, so thank you. 8)
Thank you so much for writing this article! I can’t tell you how many times I’ve had to tell my friends what to do after their email account gets hijacked. I especially liked the tip about changing the account passwords which the person used that email address to register for. It would be really easy for a hacker to search the email history for registration confirmation emails and then go back to that site and request a password reset (scary thought!).
I might also add that when in a public place like a coffee shop, make sure you’re connecting to your email using a secure connection. The user should look for an HTTPS:// address in their web browser. I know Gmail offers this by default but I’m not sure about other providers these days.
You are exactly the kind of person I wrote this guide for. There is a nice printable version of every article on ghacks. I know I will end up using it. Also, if you get spam from a friend, reply back to them with the odd message and this link. The work is done for you.
Mr. Lang, Despite using strong passwords and going through most of the steps in this article before I came across it, my email account has been repeatedly hacked in the last two weeks. Have up to date anti-virus and scans, trojan, and rootkit scanners. Everything shows ok. Do you have any thoughts as to what’s going on, or how to end this? I was thinking of abandoning this account, but either way it’s a time consuming hassle – Thank you.