Have You Read the Fine Print for the Amazon Cloud Drive?
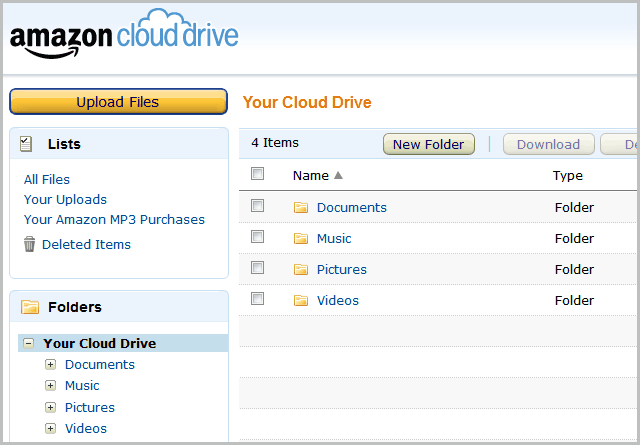
Amazon's new Cloud Drive service has made the news recently. The service allows you to store any kind of file, and even stream music loaded to it through its Cloud Player. It would be wonderful to have such a service, but at what cost? I don't mean the price, which is free, but the conditions.
All of the headlines, features, and promises have caused the public to overlook a disturbing section of the fine print in the lengthy legal agreement. As a part of using the Cloud Drive, Amazon reserves the right to look at your files. They don't have to ask or notify you. They can even keep files you delete. They can even share this information with others. This kind of clause usually mentions something about courts, subpoenas, or some other legal context. There are no such conditions here.
"5.2.Our Right to Access Your Files. You give us the right to access, retain, use and disclose your account information and Your Files: to provide you with technical support and address technical issues; to investigate compliance with the terms of this Agreement, enforce the terms of this Agreement and protect the Service and its users from fraud or security threats; or as we determine is necessary to provide the Service or comply with applicable law."
This is in striking contrast to Dropbox, a service similar to Amazon's Cloud Drive in many ways. You can upload files to Dropbox for storage through a web interface, just like with the Cloud Drive. In the Cloud Drive, files are unencrypted, easy for the company to read. Dropbox encrypts both its connection and its files, leaving only the file names unencrypted. This is to protect your privacy, but it does come at a cost. If you have a problem with a file, and an old version is not sufficient or available, then there is not much that Dropbox's tech support can do. An IT employee at Amazon would able to take a closer look to diagnose the problem. Security is often a trade off between convenience and privacy, so there is some validity in Amazon's decision.
It will be interesting to see how this plays out. Amazon's 1984 incident shocked the world, and it is in a position to take such controversy to the next level. Anyone could find files missing, information leaked, or embarrassments made public. Alternatively, they could simply delete music you own.
There are some other parts of the agreement that are note worthy, but less than alarming. You are not supposed to share access of your account with anyone else. An unsurprising, and arguably sensible, clause. With no feature to share files, as found in Dropbox, this can create problems. The only way to share a file would be with a joint account, which would not be permitted in the agreement. There also is no way to publicize a file, so you cannot use the service for any kind of web hosting. In contrast, not only can Dropbox do that, but it can generate photo albums that can be shared with just a link.
To use the Service, you must have an Amazon.com account. You may only use the Service in connection with one Amazon.com account, so if you have multiple Amazon.com accounts, you'll need to choose the account you want to use for the Service. The email address and password for your Amazon.com account are all that is required for access to files you store on the Service. You are responsible for maintaining the confidentiality of your account and password and preventing their misuse and you agree to accept responsibility for all activities that occur under your account. You may not use a name, username or email address that you are not authorized to use or share your Amazon.com username and password with others for purposes of allowing others to use the Service through your account. If we suspend or terminate your use of the Service or your Amazon.com account, you may not use the Service through another Amazon.com account.
There is one kind of file that makes sense to store in Amazon's Cloud Drive: any kind you got from Amazon. They already know you have it, so there is nothing for them to discover. Music is a prime example, and they literally have thousand of free songs. Several gigs of files can be loaded into the cloud drive in a single sitting, and new music purchased from Amazon (even for $0.00) never counts against your quota. This solves a problem that exists in other services: re-downloads. There is never a fee to download a song from your cloud drive. It effectively can be seen as an instant off-site backup. Hopefully Amazon will expand this service to other products such as games and movies.
While the privacy concerns limit the usefulness of Amazon's Cloud Drive, it does not make it useless. It would be inadvisable to store sensitive information on it, but it provides a perfect backup for files you purchased from Amazon.
Advertisement


















Bedankt voor het delen, was hier al even naar op zoek!
http://arstechnica.com/security/news/2010/01/768-bit-rsa-cracked-1024-bit-safe-for-now.ars
Quote from the paper itself:
To crack a 768-bit RSA cypher:
“We spent half a year on 80 processors on polynomial selection. This was about 3% of the main task, the sieving, which was done on many hundreds of machines and took almost two years. ”
A 1024-bit RSA cypher is a thousand times more difficult to crack. The paper suggests that the first cracking of a 1024-bit RSA cypher would happen within 3-4 years of their publication, or 2-3 years from now (April 2011). So, if you want to be safe, use a 4096-bit RSA cypher, and your file will be secure for quite a while.
Thanks for pointing out these clauses. I would definitely not store personal documents there unencrypted. I just realized though that nothing prevents me from storing an encrypted TrueCrypt file container there. Take that and read it all you want, Amazon! :)
An encrypted backup, of some nature, I might use it for, especially with a little stenography (hiding files within files) in play. The problem is, a company like Amazon has the CPU power to decrypt a file much faster that a typical person or even organization. In other words, they can retain the file, decrypt it, and then look at it all they want.
Good point about Amazon’s CPU power, I’ll have to keep that in mind. But, I doubt that even Amazon’s distributed computing infrastructure has the horsepower to break 256-bit AES encryption in a practical amount of time. The question really is why would Amazon spend that kind of CPU cycles breaking some random person’s encrypted file unless they know there is something worthwhile in there.
The TOS make the service useless for anything you consider private.
However, Ryan, your last paragraph points to the “perfect” use
for this service and for that it certainly would be.
I tried not to be to hard on Amazon in the article. I don’t think they are evil, just a bit short sighted. There are possibly valid reasons for the way they decided to go, but I haven’t uploaded a single file to the service. On the other hand, I have over a thousand songs on it already.
You were quite fair to the facts, Ryan, and that is what matters.
Amazon’s terms of service speak for themselves and for Amazon.
There may be an element of Amazon fanatically insuring
the site will not in any way become a source for
copyright infringement with file sharing.
Google had the same type of “we can use everything you upload” for gmail when they launched the x gig storage campaign. When it came to light that your work became their property to use, they changed their TOS.
Hopefully the same thing will happen here.
The thing is, there is no such thing as “free” when someone is bearing a pretty significant cost of servers to host all of this storage capacity. If the TOS is changed, look for changes that generate revenue another way.
Facebook did the same thing, too. I think the lawyers get a little over protective, so I don’t think it’s a malicious thing. Still, it’s a pattern that we keep seeing in industry.
Do they have a clause that would enable them to nuke your data if you became politically on the nose, e.g. Wikileaks and Paypal, Mastercard and Visa? Probably a silly question given Amazon did stop hosting Wikileaks quick smart.
I’m far from convinced that entrusting data, especially unencrypted data, to a third party is wise. At least not without having several local backups.
As I recall, it doesn’t outright claim that right, but that wouldn’t stop Amazon. They seem to error on the side of: “It’s easier to ask forgiveness than permission.”
Granted, I only double checked with a quick skim. The document is just too long, which is often the point.
Nice catch. People should know about this and stay on their dropbox account. I was considering to switch but i’m going with dropbox now.
I’m a Dropbox user myself. I read the fine print before I signed up, and was fine with what I saw. I also looked into how they protect your data, and that is mentioned in the article. Fact is, from strong privacy to efficient data transmission, Dropbox has done it right.