Failed Facebook Login Attempts Reveal Private Information
Facebook does not seem to come to rest these days when it comes to privacy. A new bug was discovered on Wednesday by researcher Atul Agarwal, which allowed anyone to match an email address to a Facebook user's name and profile picture.
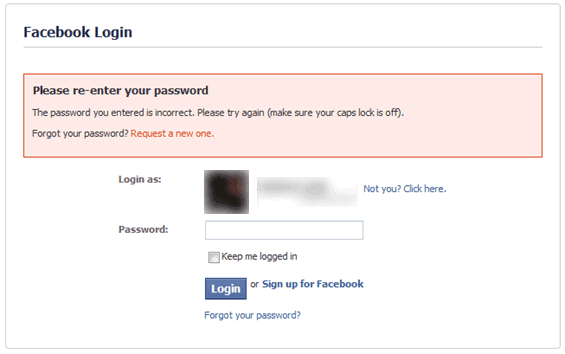
Facebook has designed the login process to provide additional information to the user if the email and password combination used to log in do not match.
Instead of just displaying a warning that the log in information were not correct, Facebook went one step further and displayed "Login As" information on the page. This included the user's profile photo and full name regardless of that user's privacy settings on Facebook.
Atul described the problem in detail on Seclists:
Sometime back, I noticed a strange problem with Facebook, I had accidentally entered wrong password in Facebook, and it showed my first and last name with profile picture, along with the password incorrect message. I thought that the fact that it was showing the name had something to do with cookies stored, so I tried other email id's, and it was the same. I wondered over the possibilities, and wrote a POC tool to test it.
This script extracts the First and Last Name (provided by the users when they sign up for Facebook). Facebook is kind enough to return the name even if the supplied email/password combination is wrong. Further more,it also
gives out the profile picture (this script does not harvest it, but its easy to add that too). Facebook users have no control over this, as this works even when you have set all privacy settings properly. Harvesting this data is very easy, as it can be easily bypassed by using a bunch of proxies.
The issue has been fixed in record time by Facebook. It does however mean that
the privacy issue was exploitable by everyone, including users without a Facebook account, until the fix had been applied.
In plain English, anyone who discovered the issue was able to link email addresses to real names and profile photos on Facebook, even without an account.
Dedicated attackers may have used automation to extract the information in bulk from Facebook.
The proof of concept code that Atul wrote showed that malicious users could have exploited the issue to create a huge database of linked email addresses and full names, which could be disastrous if used in phishing campaigns or other malicious uses.
Advertisement




















just wondering why facebook is having a lot of trouble today its doing alot people heads in and mine its just so slow.and its even on my phone.i do love facebook keep in contract with people and family who live miles aways.so please lets us know what what,thankyou,
my facebook hacked by some body..please let me know who and how to fix it?
Hey facebook why have i failed to login help me out i really need to sign up for facebook. Direct me on how it iz done.
You are very good
This problem is not fixed!! I tried making wrong password attempts with my accounts and after a captcha secruity check i was taken to the same page, revealing my profile pic, name and email address…
This is WAY over my head except for the fact that I have been trying for 4 days to get my password reset with no results. I have gotten a few emails from facebook & have been told those might not be real. I am at my wits end here. I am not a big social networker but I do want either access to my account to use or close. Is facebook just that behind or have I been hacked, Thanks for any help.
Tari, it never takes that long to reset a password. You need to take a closer look at the links in the password reset emails, if the point to facebook.com then all is well. You can usually check those by hovering with the mouse cursor over them and looking in the status bar of the web browser or email program.
How is this different from searching for emails on facebook? When searching for a email, you also get a picture and the persons full name.
But using the exploit/bug you could “match” a email with a picture and a name, right? Why not just search for the same mail on facebook and get the same result? Or am I misunderstanding something?
HNicolai, the difference is the account. The login method did work without a Facebook account, which means attackers could exploit the issue with a lot of time and a simple script. I have not tried the search in Facebook, but it probably limits the requests per x minutes or something like that. It would also mean that automation would be more complex, if not completely impossible.