Apple Leads In Security Vulnerabilities, Microsoft Third
Apple software had more reported security vulnerabilities than any other company in the first half of 2010, according to security company Secunia, a reputable security company that tracks security vulnerabilities since 2002.
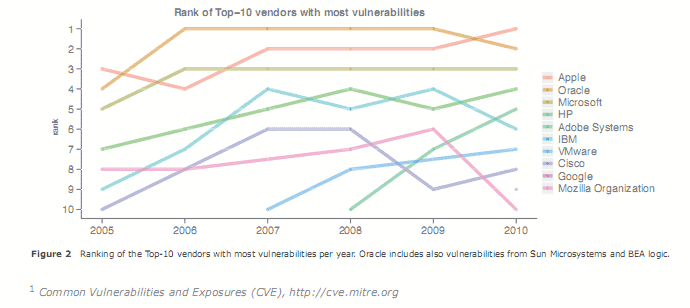
Last years leader, Oracle, dropped to second spot while Microsoft managed to retain the third spot firmly in the last five years.
Adobe made their first appearance in the top ten in 2008, and managed to climb to position five in this report. Lastly, Google is now ranking on position nine in the listing, displacing Mozilla, which now ranks on ten.
To gain more insight into the security ecosystem we identify the group of the ten vendors with the most vulnerabilities (in all their products) in any given year. Since 2005 these Top-10 vendors are responsible for about 38% of the total vulnerabilities representing 16% of the Secunia Advisories per year. The composition of the Top-10 group varied only slightly in this period; seven of the Top-10 vendors with the highest vulnerability counts in 2005 are still in the Top-10 group in 2010.
The total amount of security vulnerabilities was used to create the report, with severity ratings playing no role in the rankings. This means that software from a company with more vulnerabilities does not necessarily have to be more insecure. The trend however is obvious. The graph shows a clear jump in rankings for Adobe, a company that is struggling to keep up with patching security vulnerabilities in its flagship products Adobe Reader and Adobe Flash.
Attackers have noticeable shifted attacks from operating systems to third party software, and Apple, along with Adobe and Oracle, happens to produce several popular programs, including iTunes, Quicktime and the Safari browser.
Speaking of Safari, an Autofill vulnerability has just been uncovered that allows websites to uncover private information.
Right at the moment a Safari user visits a website, even if they’ve never been there before or entered any personal information, a malicious website can uncover their first name, last name, work place, city, state, and email address. Safari v4 & v5, with a combined market browser share of 4% (~83 million users), has a feature (Preferences > AutoFill > AutoFill web forms) enabled by default. Essentially we are hacking auto-complete functionality.
Attack vectors have been analysed by Secunia as well. Remote attacks are still on the rise while local network and system attacks slowly declining.
We observe that “From remote†is consistently and by far the most prevalent attack vector (81% in average), compared to “Local system†with 9.8% and “Local network†with 8.2% in average over the last five years. Thus, most of the vulnerabilities expose the user of the software to remote attacks. Based on the data available by mid 2010 we do not expect a change by the end of the year.
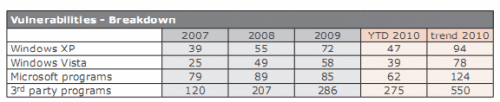
In every report, Secunia analyses a typical Windows PC environment (both Vista and XP) with a top-50 software portfolio consisting of 26 Microsoft and 24 non-Microsoft programs.
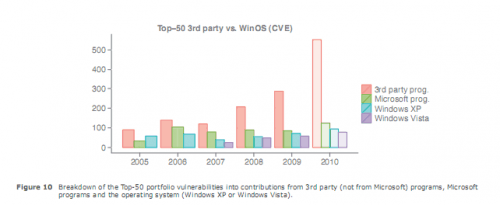
The analysis confirms the growing trend of exploiting third party software.
The vulnerabilities breakdown shows an overall increase in vulnerabilities on both systems. The vulnerabilities disclosed in Microsoft programs rose by about 50%, from 85 in 2009 to now 62 in the first half of 2010, with a projection to end at about 120 vulnerabilities.
The third part programs increase is earth shattering. From 286 vulnerabilities in 2009, to 275 in the first half of 2010 and a projected total of 550 at year end. That's a 100% increase, and more than four times as many vulnerabilities as in Microsoft programs.
The next figure visualizes the increase in third party software vulnerabilities.
Mozilla Firefox tops the vulnerability listing with 96 reported vulnerabilities, followed by Safari with 84, Java and Google Chrome with 70, Adobe Reader with 69, Adobe Flash Player and Adobe AIR with 51, Apple iTunes with 48 and Mozilla Thunderbird with 36.
The top Microsoft programs are Internet Explorer with 49, Excel Viewer with 37 and Excel with 30.
Typically, a user can patch 35% of the vulnerabilities with one update mechanism (Microsoft’s), and needs to master another 13 or more different update-mechanisms to patch 65% of the 3rd party program vulnerabilities.
Interested users can access the full PDF report over at the Secunia website.
Advertisement
















All the security vulnerabilities in Apple don’t effect even one Mac, while every single one of Windows security vulnerabilitiy effects Billion PCs.
“security vulnerability”
Read the 1st word, SECURITY. It affects Apple, which means its products.
For Microsoft it affects its products same, which products doesn’t matter.