How to add users to /etc/sudoers
If you've worked with a Linux long enough, you will have come in contact with the sudo utility. What is sudo? Sudo has been brilliantly described by the XKCD comic here. What sudo does is allow a user to run commands and applications with the security privileges of another user. Most often this is used in distributions where the root user has been locked out and then gives the standard user the privileges to do things like install applications or run applications that would normally require administrative rights. For example: When you want to restart networking you would normally run the command /etc/init.d/networking restart as the administrative user. But without being able to log in as the administrative user, you would instead issue that same command like: sudo /etc/initi.d/networking restart. You would be asked for your users' password and networking would restart.
But what if, as a system administrator, you add a new user and want to give them similar sudo rights? How do you go about doing this? Could you just open the /etc/sudoers file in your favorite text editor and make some changes? No. There is another tool that you must use called visudo. The reason for this is that the visudo command ensures that only one person can edit the /etc/sudoersfile at a time (in order to avoid any possible security or user-induced overwriting issues). As the name might imply, visudoers will default to the vi editor. But if you have set up your installation to use a different editor (such as nano), visudoers will default to that. With that in mind, let's make some changes!
As you might expect, you can't just issue the visudocommand without using sudo itself. So to actually open your /etc/sudoers file with visudo you must issue the command (from within a terminal window):
sudo visudo
NOTE: If you have Phil Collin's song Susudio playing in the background, you will still have to use sudo when using the visudo command.
When you open visudo you will immediately notice it is not an overly huge file (approximately 25 lines long). Â You will also notice near the end a section that looks like:
# %sudo ALL=NOPASSWD: ALL
You might be tempted to uncomment this out so you no longer have to type that sudo password. DO NOT DO THIS or you will compromise the security of your system.
There is a line a few lines above this that looks like:
root ALL=(ALL) ALL
What you need to do is mimic this line just below it with the new line to include your new user. This new line will look like:
username ALL=(ALL) ALL
Where username is the actual username you have added.
Isn't there a GUI?
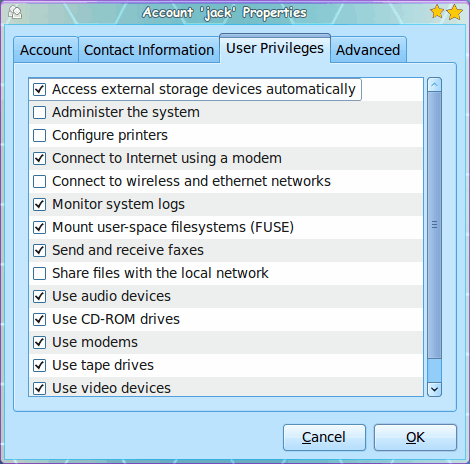
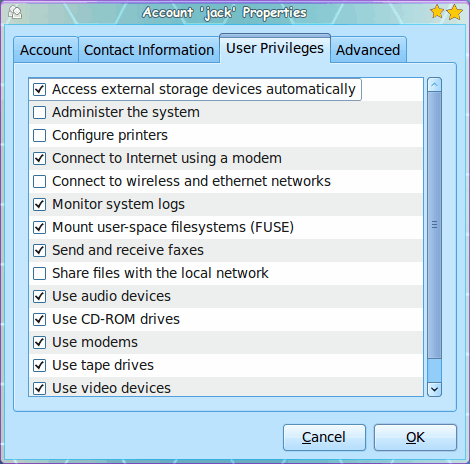
Yes, there is. If you go to the Administration sub-menu of the System menu and select Users and Groups you can unlock this tool (click the "Keys" button and enter your password). Now select the user you want to modify and click the Properties button. Figure 1 shows a new user without Administrative (sudo) rights. Click the check box next to Administer the system and then click OK. Â This user should now have the same rights as they would have by using the visudo command.
Me? I prefer doing things the command-line way, simply because I feel there is more control. But if you prefer the GUI path, you can have that as well.
Final thoughts
As always, use caution when giving users administrative rights. If you don't trust their skills or their motivations, don't give them the ability to bring down your system.
Advertisement















Hi,
In order to be able to “sudo” again , how could I get back the administrator password that was changed into standard
regards
Budi M
A very useful feature is to allow specific programs to be run through sudo without being prompted for a password.
On my home machine I have a small script that runs aptitude and, generally being too lazy to enter a password, I have authorized myself as follows:
jason ALL=NOPASSWD: /usr/bin/aptitude
Make sure you use ‘whereis’, or equivalent, to get the correct path.
There is an error in your article. You state that you cannot just open the /etc/sudoers file in a text editor and make changes. This is not true. While using visudo is strongly recommended, it is not required. The advantages to using visudo over some other text editor are:
1. It will do syntax checking and refuse to save a broken sudoers file.
2. It does file locking so that only one person at a time can use visudo to edit the file.
The problem with the file locking is that it doesn’t prevent someone from just opening the file in some other editor and changing it while visudo is running.
You can even write custom Perl or other scripts that do modifications to /etc/sudoers for you when you create new user accounts.
“1. It will do syntax checking and refuse to save a broken sudoers file.”
are you sure, txttechdog?
# visudo
>>> sudoers file: syntax error, line 26 <<<
What now? h
Options are:
(e)dit sudoers file again
e(x)it without saving changes to sudoers file
(Q)uit and save changes to sudoers file (DANGER!)
What now? Q
visudo also protects against configuration errors by the visudoer :
# visudo
>>> sudoers file: syntax error, line 26 <<<
What now? e
..
heh, I also like Phil Collins ;-)
Thanks for this great and funny article!
Note that the GUI-tool mentioned is not a front-end for sudo management. It only handles memberships in OS-groups (/etc/group) and relies on sudo being already prepared with the following line in /etc/sudoers
%admin ALL=(ALL) ALL