Microsoft Rogue Detection Tool
Rogue DHCP Server Detection Tool has been created by the Microsoft Windows DHCP Team to provide system administrators and users with a tool to detect rogue DHCP servers in computer networks.
The team that created the application classifies rogue DHCP servers as servers that have been unintentionally misconfigured, unauthorized unknowingly or configured with malicious intent. The impact of these servers on clients that are served by the server can be quite critical; it includes scenarios that lead to network access problems and opens the door for network traffic sniffing.
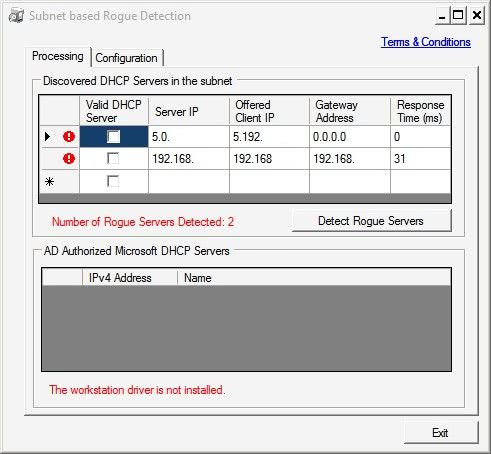
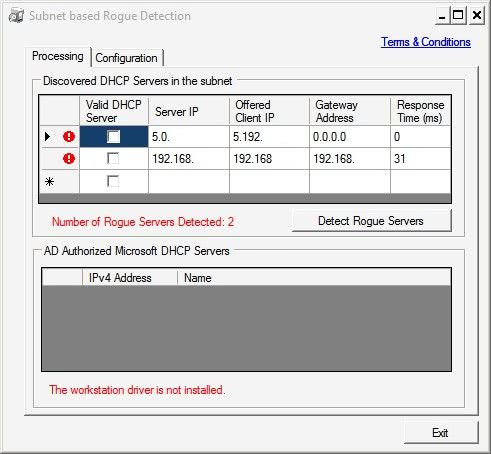
The security program that Microsoft released is a portable application that can be started right after downloading it from the Technet servers. It displays a graphical user interface that lists all discovered DHCP servers.
A click on the Detect Rogue Servers button is required to initiate the scan of the computer network to detect servers that are potentially misconfigured or rogue.
The Microsoft Rogue Detection Tool displays all DHCP servers in the list that it considers rogue servers (It is not clear if it classifies all servers as rogue servers in the beginning). Information like the server IP, gateway address and offered client IP are displayed in the list. It is possible to check the valid DHCP server box to classify the server as a valid server which will make that information persistent.
The program can be configured to run once or at specified intervals. It is furthermore possible to select only specific interfaces. Currently only IPv4 interfaces are supported with plans to add IPv6 interfaces in the future.
Microsoft's Rogue Detection Tool can be downloaded from the announcement page over at the DHCP Team blog.
Update: The post on the Microsoft DHCP Team blog is no longer available. We have uploaded the latest release version of the Microsoft Rogue Detection Tool to our own server for archiving purposes. Please note that we don't support the program in any way. You can download the application with a click on the following link:Â (Download Removed)






















I cannot find it on page specified or doing a search. Is this still available?
Awesome. There are few things that make huge network go haywire faster than some stupid stupid router imaging itself to be domain DHCP server. :)
Will have plenty of use for this one, thanks!