Force SSL HTTPS Connections In NoScript
SSL connections, which you can identify by the use of the HTTPS protocol in the address bar of the web browser that you are using, provide additional security in comparison to the HTTP protocol.
Basically, what this means is that the connection is encrypted to protect the flow of data. New versions of HTTPS offer additional benefits.
This is why many companies use SSL on security sensitive pages of their website or the entire site. While secure sites are often found in the financial sector, quite many sites and services have implemented it on sites that are not related to the financial sector at all.
To put it bluntly: A bank not using SSL on their website cannot be trusted. HTTPS connections are encrypted which means the traffic is being protected from local network sniffers. There are however still attack points like keyloggers or viruses on the user's system.
There is one additional problem concerning websites that do offer HTTPS connections on most of their network but not everywhere. Mouser over at Donation Coder mentioned a hidden setting in the NoScript (check my Firefox security profile for additional information) add-on of the Firefox web browser that enables you to force HTTPS connections for listed websites.
This is helpful in a few cases. Some websites offer both HTTP and HTTPS connections to their servers, but no option to make one or the other the default.This is often the case when sites test HTTPS but have yet to make a decision on enabling it solely. Another possibility is that websites make use of HTTPS connections but not on all pages.
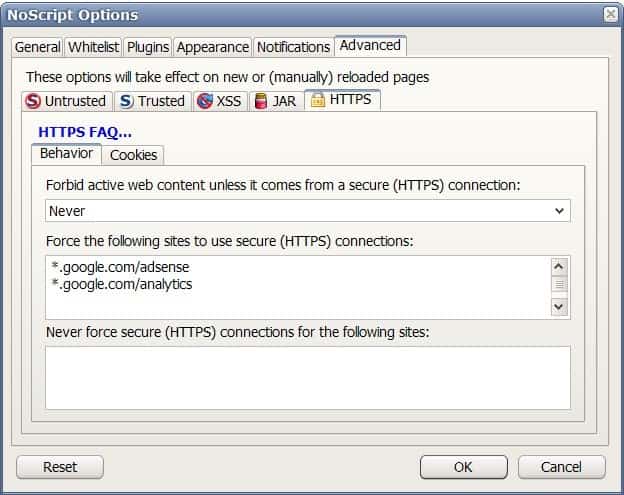
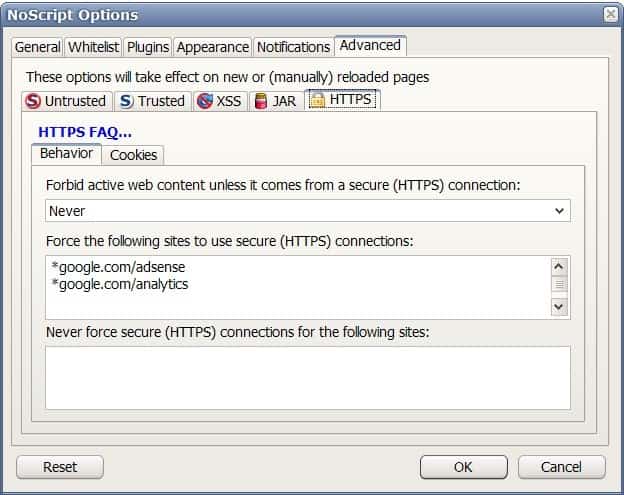
Users with the excellent NoScript add-on installed can configure sites to always use a secure https connection when they are visited. This option can be enabled by right-clicking the NoScript icon in Firefox, selecting Options from the context menu, clicking on the Advanced tab in the configuration and there on the HTTPS tab.
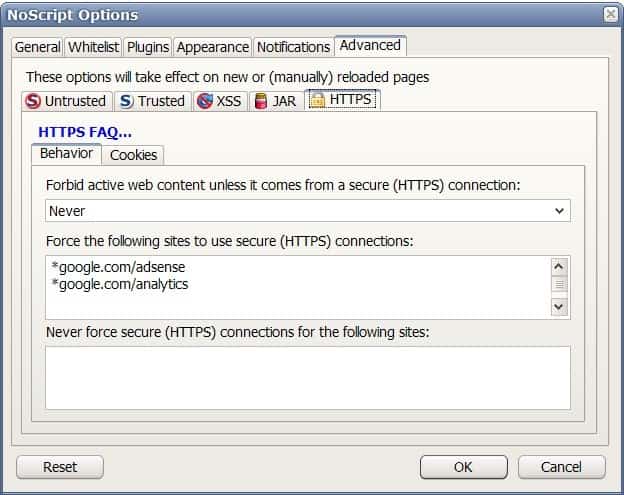
New websites or pages that should be forced to use secure HTTPS connections can be added to NoScript in there. The use of wildcards is supported as well.
Users should however note that this will not work on all websites. It will obviously not work on websites that do not offer HTTPS. There are also sites that automatically redirect HTTPS requests to HTTP. Google.com is a prime example of this. If you add google.com to the list you will notice a never ending loop when opening that website because of NoScript trying to force HTTPS and Google redirecting to HTTP.
Update: The Google example is not up to date anymore as Google is now enforcing HTTPS on the majority of company properties. NoScript on the other hand can still be configured to enforce HTTPS connections as described in the guide above.
You may also block the use of HTTPS on select sites using the NoScript feature. This is usually not recommended though as you reduce the connection security this way.
An alternative to using NoScript is to use HTTPS Everywhere instead which is available for Firefox, Chrome and other browsers. The add-on's sole purpose is to enforce the use of HTTPS on sites that don't run on it fully.





















Awesome tip Martin – I never even knew that setting was in there! I once tried writing an extension to do the same thing and I could never seem to get it to work. This is perfect.