USB Port Protection
USB Blocker is a free program for Microsoft Windows devices that enables you to block USB ports on the computer to improve security.
System administrators do not only have to make sure that the computer systems that they administrate are protected from online threats: local attacks are also a common threat that computer systems have to be protected against.
One prominent way of gaining access to a local computer system is by connecting external devices to the system. USB ports have to be blocked by system administrators so that external devices cannot be connected to those systems.
Some of the dangers are malware threats that could be distributed in a computer network from one entry point or data theft by copying data from the local system to a removable device.
USB Blocker
USB Blocker is a software program that can protect USB ports from being accessed without authorization. One main benefit of USB Blocker is that it relies solely on group policy mechanisms and does not have to be deployed on client computer systems. USB port protection can be achieved with just a few mouse clicks on connected computer systems.
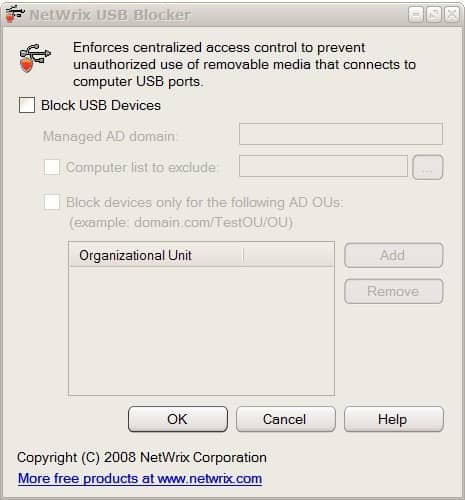
The application is controlled via a small interface that pops up right after installation. A click on the Block USB Devices checkbox enables the options for managed active directory domains and provides the means to exclude computers from being blocked by the USB port protection software. There is also an option to only block devices for specific organizational units in the Active directory.
The usb port protection software can only be downloaded after a quick registration (without verification) at the website of the developer. USB Blocker is compatible with most Microsoft operating systems. A commercial version exists as well which extends the functionality of the USB port protection to include additional devices among other things.
Verdict
USB Blocker requires quite some testing to get it right before you deploy it on your organization. While the blocking itself requires little effort, as you only have to enable the feature, set a domain, and optionally computer systems that you want excluded from the protection, it is recommended that you test the protection by connecting various types of USB devices to protected computer systems.


























thank you very match
I really disappointed, we can disable access to usb devices through group policy editorand also through registry,what’s use of this only disabling usb devices instead I want a freeware which allows my usb drive and prevent other usb drives from entering into my system ,are there any freewares available like them to authorise the use of usb devices.
This is a nice little tool and have used it and reviewed it myself. It would be handy for owners of internet cafe’s or other public computers.