Encrypt Thunderbird Email with Enigmail
Sometimes email contains sensitive data which must be encrypted. You can handle this two ways, manually encrypt the data or use an exceptional Thunderbird Extension called Enigmail. This extension uses gpg and makes the encryption/decryption as user-friendly as it gets. With keys installed in Enigmail (either manually or from a keyserver) encrypted email is automatically decrypted and signatures are checked for validity. This makes using encryption for email a task even the new user can master.
If you do not have a key pair generated, Enigmail can even do this for you. So with this extension you can encrypt/decrypt email without having to touch the command line. Pretty sweet. Let's take a walk through this system.
I am going to assume you know how to install an extension in Thunderbird (I am also going to assume gpg is installed). Knowing that, install the Enigmail extension. Once this extension is installed (and you have restarted Thunderbird), you will notice a new menu entry called OpenPGP. This is where you take care of the setup of Enigmail.
Generate your key pair
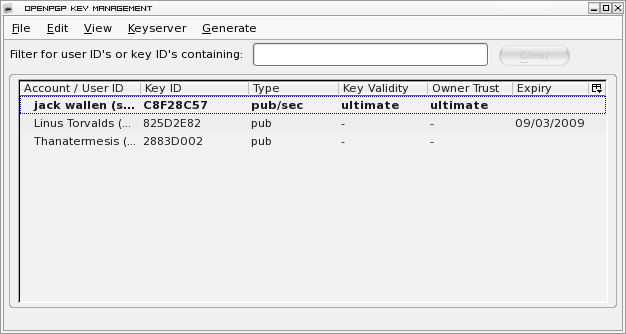
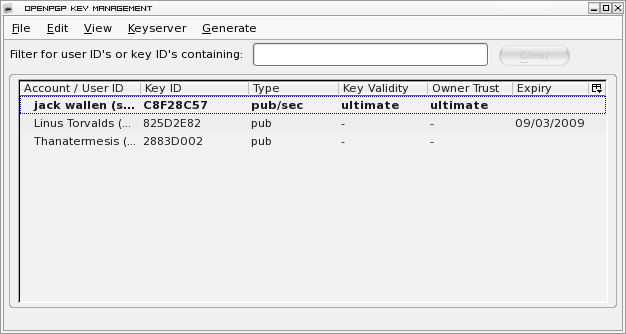
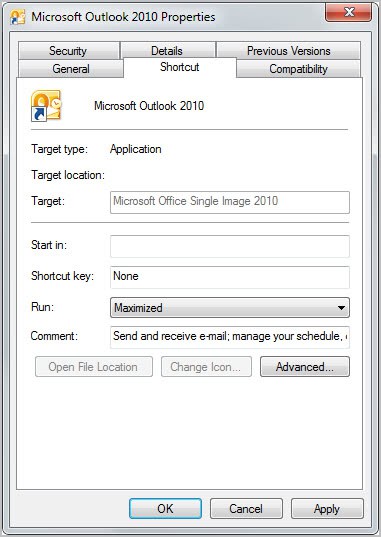
The first step is to generate your key pair. This can be done either from command line or from Enigmail itself. From within Thunderbird click the OpenPGP menu and click the Key Management entry to open the key manager window (shown in the image to the left.)
Click on the Generate menu and select New Key Pair to open the key generation window (shown below to the right.)
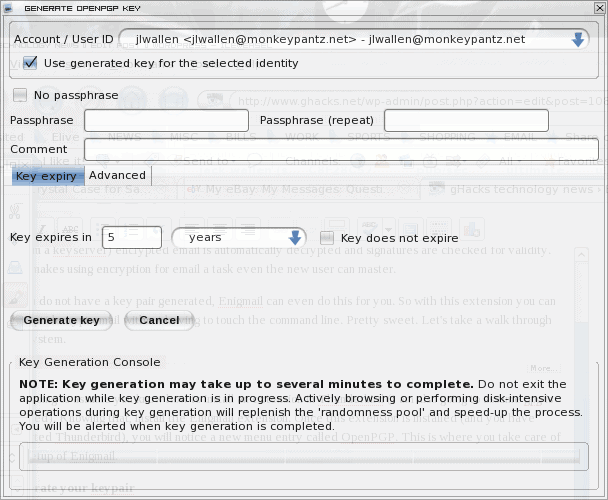
From within this new window you have a number of options to consider (which are all fairly self explanatory.)For most instances the defaults will work. The only change you might make is if you do not want the key to expire click the Key Does Not Expire checkbox.
As the window says, during the generation process you will want to go about the business of using your PC in order to help randomize the process of key generation. This even holds true when you are generating keys via the command line in Linux.
If you already have a key on your machine (generated from the command line or some other tool) you can import that key from the same key manager tool shown above. Just click on the File menu and select Import Key from File.
Once your key has been imported into (or generated by) Enigmail you are ready to use Enigmail to encrypt your messages.
Encrypt and Sign a Message
Start composing a new email and you will notice the OpenPGP menu entry has been added. Once you have completed composing your email click on the OpenPGP menu and select Encrypt Message and/or Sign Message to encrypt and/or sign your outgoing messages with your key.
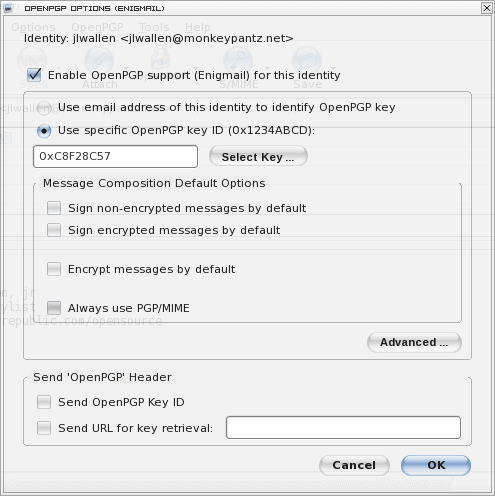
This brings up an issue. If you do not configure Enigmail to not encrypt/sign by default all of your outgoing messages are going to be encrypted and signed. This is a problem when the recipient doesn't have your key. I highly recommend configuring Enigmail to not encrypt/sign by default. To set this click on the OpenPGP menu entry in the MESSAGE COMPOSITION WINDOW (not the main Thunderbird window). From there click on the Default Composition Options sub menu and then select Signing/Encryption Options. A new window will appear (shown to the left.) Make sure you de-select all of the options in the Message Composition section. Now you have to manually choose to sign and encrypt each message. It's one extra step but your non-geek friends and family will thank you for it.
Decrypting
Like send mail, you have two options for receiving mail. You can have encrypted mail automatically encrypted or you can do it manually. Of course for either options you have to have the senders' key imported into the system.
If you click on the OpenPGP menu (in the main Thunderbird menu) you will see an entry for Automatically Decrypt/Verify Messages. If this is checked all incoming encrypted/signed mail will be decrypted/verified. If it is not checked you will have to do this manually by selecting the encrypted/signed email and then clicking the Decrypt/Verifyentry in the OpenPGP menu.
Final Thoughts
And that's it! Simple email encryption in Linux with Thunderbird and Enigmail. You can, of course, do this manually from the command line, but why make things difficult? If you have needs to encrypt/sign outgoing or incoming email, Enigmail is the perfect solution for every Linux and Thunderbird user. And for those BSD, Solaris, OS/2, Mac, or Windows users there is an Enigmail for you as well.
Advertisement

















As I understand it public keys can be transmitted in the clear, there is no need to encrypt them? For instance, if I want to let people send to me encrypted mail, I could publish my public key on my website?
Dotan yes it can basically be published anywhere.
I see, thanks. That’s actually quite clever on the part of the devs.
Dotan that’s how public key encryption works. The main problem that you have is to exchange the keys in first place which is the requirement to be able to encrypt messages. It does also mean that all communication is unencrypted if public keys have not been exchanged.
How much harder will it be for the reciever to decrypt the messages? Will they have to install special software? Do Gmail and other online email clients support this? What about Outlook users? If they are in a corporate environment and cannot install plugins, can they still read the mail?
Dotan while I cannot answer all questions I can answer some. A sender can only encrypt messages if he got the public key of the recipient. This means that you can obviously only send encrypted messages to recipients who have a public key which means they need to have a compatible plugin or software installed.