Track your stolen computer with Locate PC
If you travel a lot chance is that you will eventually fall victim to theft. If you happen to have your notebook or laptop with you most of the time chance is pretty high that the thief will have the desire to steal that one. Chances are pretty slim that you will see your notebook again after the theft but you can increase them a bit by using Locate PC.
Locate PC only works if the thief is stupid enough to boot your computer while being connected to an internet connection. I cannot really say how many thiefs would do that but it can happen and that's probably reason enough to use Locate PC. A slim chance is better than no chance at all, don't you think ?
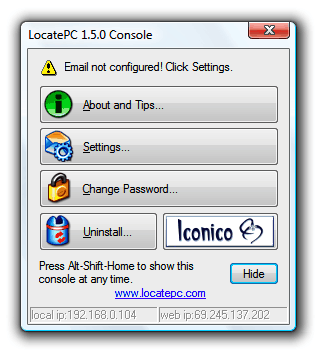
Locate PC (via Cybernet News) will send emails periodically whenever the PC is connected to the Internet, by default one email is send per day and another one for every IP change. The application is running in the background with an obscured filename and no system tray icon making it harder to identify. I would say that you do not need to worry about that though, if the thief really boots the PC while it is connected to the Internet then you should not fear that he will discover the little tracking application.
One thing that actually might work pretty well is to create a bogus account that does not require a password. I mean, a thief that gets a password prompt will probably not be able to load the operating system which would make the whole configuration void.
The emails that are send contain several interesting information, not only the IP that it is being send from. It displays the computer's host name and logged in user. This will be probably your information though. More interesting are the network connections that are listed. A dialup connection would reveal the phone number and the user name which can lead directly to the thief.
A traceroute command is issued as well and identifying information are pulled from Windows. The important information that can lead to the thief are the IP address, the network connections and the traceroute command. Everything else will be your information unless the thief decides to chance the name and address of the owner to his own.
Advertisement





















i am shreyash please help me because i am very poor and my family is deid and i am is alone
As I know there are 3 methods how to detect location of laptop:
a) GPS
b) IP detected on server computer (from which we can obtain ISP and username or new user)
c) ISP and username of new user detected by monitoring agent on client computer and reported to server computer (IP detection not used)
Which methods this program is using?
Well the program runs on the computer and detects if the IP changed. If it did it will send an email. It will also send an email once per day.
Please locate the pc registered in the name of principal,peoples college,buguda
Thanks for the great writeup! I was doing some SEO checking, and it’s funny how you show up before us! Hopefully, it won’t be that way for long. :)
– Molly.
Front end web developer for LocatePC
The newest version of LocatePC:
Recovering the physical laptop and data are the basic functions of LocatePC. http://www.locatepc.net
Additional features include:
Video Snap Shot – If a person has a camera connected to their laptop, LocatePC will take snap shots every 30 seconds of the person and/or everything in the room. It will then add the pictures to the LocatePC Control Panel with a date and time stamp.
Key Logging – The ability to record all the keys the thief types. For instance, if they go to their Facebook page or decided to Twitter, a person will have the ability access their real name, username and password.
Text Message –The ability to set your computer to text message your cell phone or email you every time the computers IP Address changes.
Text to Screen- The ability to send a message to your computer screen that the thief can read.
Shut Down – The ability to have the computer shut down every time the thief turns your computer on.
Inventory – Nothing more of a headache, than to try to take inventory of the hundreds or even thousands of computers. LocatePC will take a detailed inventory of all your computers whether they are in your office, in the field, the United States or internationally.
“The U.S. Federal Trade Commission recommends using tracking devices like LocatePC which can help track down the location of a stolen laptop. We are excited about this product launch and know this product will benefit our customers.â€
My computer was stolen in georgia
Ha! If computer stolen it will continue to check for emails automatically. If you contact email server they will tell new IP address and MAC address of your laptop.
I think police already using that …
Proofread your posts! “Track your stolen computer with Locate PC” is full of typos poor grammar and bad “Engrish”!
Ask a friend or colleague that speaks and writes English to help; Are you using Google translator ?
“The emails that are send (SENT) contain (CONTAINS) several interesting (delete several interesting and substitute valuable) ….
Good share,Attractive enough for me,thanks for your kind share, laptop tracking software can help you track you stolen laptop or mobile,I have to tell you that it will be your best choice.
Try and p[revent the pc from leaving. Have a look at the above website.
The laptop is a LENOVO Think Pad and I even tried to get the company to see if they could track it and lock it and they said there was no way they could. What do I DO?
Hello my laptop that was issued to me from school was stolen and i HAVE ALL THE NUMBERS ie. manufacturer numbers serial numbers and all that and I a police report how do i Track this computer?
i have a serial number i wondering if you could track this laptop YK3V002938
what if th epc have being stolen before now
I want that software
Sounds gud!!
Thank you for da info!!
guess the tricks with webcams etc work only as long as it’s a novelty
booting with CD/DVD would stop it
solution would be intregration into the BIOS, but even that is not perfect (re-flashing/swap chip)
i keep pics of all my components so i have all serial/model # avail if needed
Hi Martin,
What you said above is right, only the dumb or the naive can ever think of such an idea. We can create as many bogus accounts like Admin of whatever as we like, but what’s the point in doing it. Maybe some years before, may be thieves could have thought about that, but in the present day, a thief who can stole the PC do very well know why and what for he is steeling the PC. So it does not matter how much we try to impersonate, the person who does it always find a way out….
Techbuzzard: The bogus account should be the first, probably named admin or something that requires no password. I think that thiefs would actually try to boot the computer or connect the computer to another one to snoop on the hard drive contents for other valuable information before they format the hard drive.
But it’s only the dumb that will fall for this. There is no real way to make sure you get your notebook back if the thief knows what he is doing.
Seems like an interesting idea to track or locate laptops or PC’s which are stolen. But there are quite a few limitations here. On the one hand the thief needs to log-in and connect to the Internet for the software to get activated. But I do not think the thieves are so naive so much that they will connect to the Internet with a stolen PC. The first thing that they will do is format the drives and install a fresh OS rather than use the existing one. The other thing is that you mentioned is to create a bogus account. I do not think it makes sense because, unless and until you have all the user ID’s mentioned in the welcome screen (that’s an option), the thieves do not have a chance to try all the ID’s and get into the system. People who really care about their systems and their data would have easily disabled that option. It’s a technological limitation that this software gets invoked only when a person logs into the system and connects it to Internet. I would like that the BIOS should include the credentials of the owner like mail ID or other details, and once booted, it should run some program in the background which connects to the real owner through emails or mobile messages indicating the correct IP address and the location once the system gets connected to the Internet. Well, there are quite some loopholes in that too, but let’s assume that a technology will come wherein the BIOS can be reset or updated by the real owner. This is just my personal opinion and anyone has the right to contradict on this.