Defeat Keyloggers with Keyscrambler for Firefox
Keyloggers are a serious threat for all computer users, but especially for users who work with sensitive data, do online shopping or any other kind of financial or security related activities on the Internet.
The biggest threat in regards to keyloggers comes in my opinion from trojans, viruses and other malware that log keystrokes once they are running on a system. There are other possibilities though how keyloggers can be installed on a system including hardware keyloggers that are added to the PC or local hacks (Check out how to defeat most keyloggers, including hardware keyloggers, to verify that none are installed on your PC).
Keyscrambler for Firefox is an add-on that encrypts the keystrokes on the keyboard to decrypt them again in the browser. This ensures that keyloggers can only log the encrypted keystrokes which protects the original data. Every time you enter data in a sensitive area an overlay is displayed which displays the encrypted keystrokes. The data is of course encrypted and entered correctly in the form to ensure that you can use the service as usual.
This add-on seems to be only working with Windows because it installs some additional files during the installation of the add-on which open a normal windows installation dialog. I did not experience the troubles that other users experienced while using the extensions. It ran without any issues during tests.
Update: KeyScrambler has been discontinued. The Keylogger Beater add-on for the Firefox web browser is an alternative.
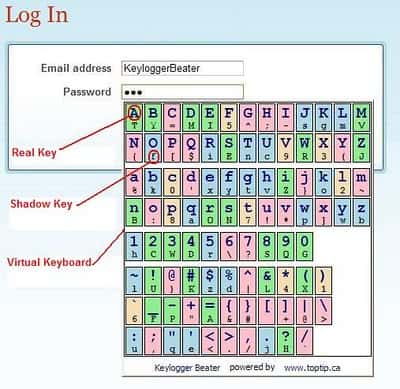
Once you have installed Keylogger Beater in Firefox you can activate the extension with the shortcut Ctrl-Alt-k. You will see a virtual keyboard attached to all forms that you click on in the browser. You can hide the virtual keyboard at any time with the Esc key.
If you want to enter something in the form, you have two options to do so. You can use the keyboard or the mouse to do just that. As you can see on the screenshot above, the virtual keyboard displays real and shadow keys, and you basically need to type the shadow key on your keyboard to enter the real key in the form. A keylogger logging your input will only log the shadow key that you have pressed, and since those change with every loading, it is impossible to link shadow keys to real keys once the virtual keyboard has been closed.
The only option that attackers have is to not only log the keys that you press but also to take a screenshot of the key map so that real keys and shadow keys can be linked to each other.
Advertisement


















Initially i had problems of popups constantly telling me to update when i was using the latest version but, after doing a full restore unrelated to keyscrambler, i installed it as a firefox addon from the firefox site…is that the reason all the issues stopped…i don’t know, but i’ve now been using keyscrambler personal for close to a year and the only problem is that on occasion it will type out the encrypted characters…but just backspacing and retyping takes care of that. So, i consider that a minor issue. I would recommend this software.
After ZoneAlarm ForceField was installed, the actual bank log-in details were appearing in the KeyScrambler Encrypted Keystrokes window on the top and the encrypted keystrokes were appearing in the bank log-in fields in the bank website.
We appreciate the review of KeyScrambler you published last December, but with the publication this year of KeyScrambler 2.0, we’d now like to update your information. The free Personal version of KeyScrambler 2.0 protects everything you type into Firefox, Internet Explorer or Flock against keyloggers, not just login information, and all websites, including online banking, online shopping, web email, forums, and more. KeyScrambler Professional now protects 15 major browsers and 19 major email and instant messaging clients against keyloggers as well as email and IM/VoIP. It costs $29.99. Thanks for your support.
Great utility but I don’t like the way the plugin reduces the size of your browser screen.
At last some addon has come to protect from keyloggers.Thanx for informing us.